How to Monitor Remote Employee Activities with Citrix Employee Monitoring
Need solutions for tracking end-user activity in your Citrix environment? CurrentWare is a Citrix Ready partner with solutions for user activity monitoring, web filtering, USB device control/data loss prevention, and remote PC power management.
CASE STUDY
Activity Insights in Citrix Workspace Drives Software Adoption and Productivity
How to Report on Remote Worker Activities in Citrix
The CurrentWare Suite is the best third-party monitoring tool for tracking employee productivity in a Citrix environment.
So long as the virtual desktops in your environment are Windows-based you can use CurrentWare to monitor and control the computer activities of your end-users. You can also monitor employees that remotely connect to an on-premises endpoint via RDP.
When monitoring employees in Citrix with CurrentWare you can track computer activities with PC Mode to track the individual virtual machine or with User Mode to track the activities of specific employees across multiple devices and/or virtual machines.
With CurrentWare you can…
- Track websites visited by employees
- Track employee logon and logoff times
- Block unauthorized USB storage devices
- Monitor what applications are being used
- Audit file transfers to portable storage devices
- Restrict internet access based on content category, domain, or URL
- See how long was spent on websites that are productive, unproductive, and neutral
These user activity reports are the perfect complement to Citrix’s performance monitoring tools. By monitoring employee activity in your Citrix environment you have the ability to enforce acceptable use policies, improve employee productivity, and ensure that your remote employees are focused on their tasks.
Track Remote Employee Work Hours on Citrix
Using enPowerManager’s User Logon History report you can audit logon events on the virtual machine. Tracking employee login activity allows you to correlate time spent working remotely with the hours that employees self-report.
This report shows you
- Which users connected to a certain virtual desktop
- Their logon time and date
- Their logoff time and date
- The duration of their logon session (logon-logoff time)
enPowerManager also includes a Startup and Shutdown History report to track each time a remote user alters the power state of their virtual desktop.
This report shows you
- Startup Events
- Sleep/Shutdown Events
- Hibernate/Standby Events
Using these reports you can track how long users have been connected to their local computers, remote workstations, and/or virtual machines.
This allows you to
- Verify that employees are starting and stopping their work days at expected times.
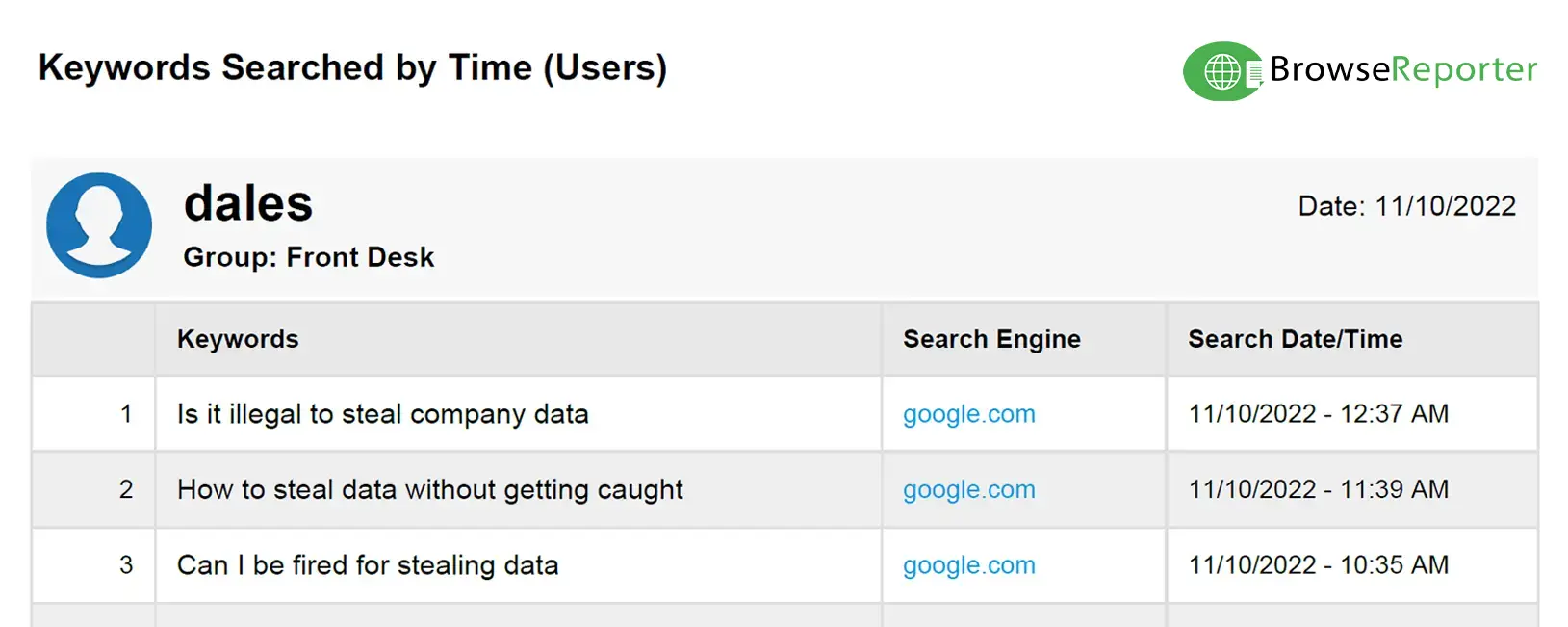
- Audit remote connections for off-hours access (potential insider threat risk)
- Compare logon times to BrowseReporter’s computer activity reports to see how they spend their time during work hours
To better track how your employees spend their time at work, you can track idle time with BrowseReporter. BrowseReporter’s automated employee time tracking features will show you whether the employee was actively using their computer during the day based on their keyboard and mouse inputs.
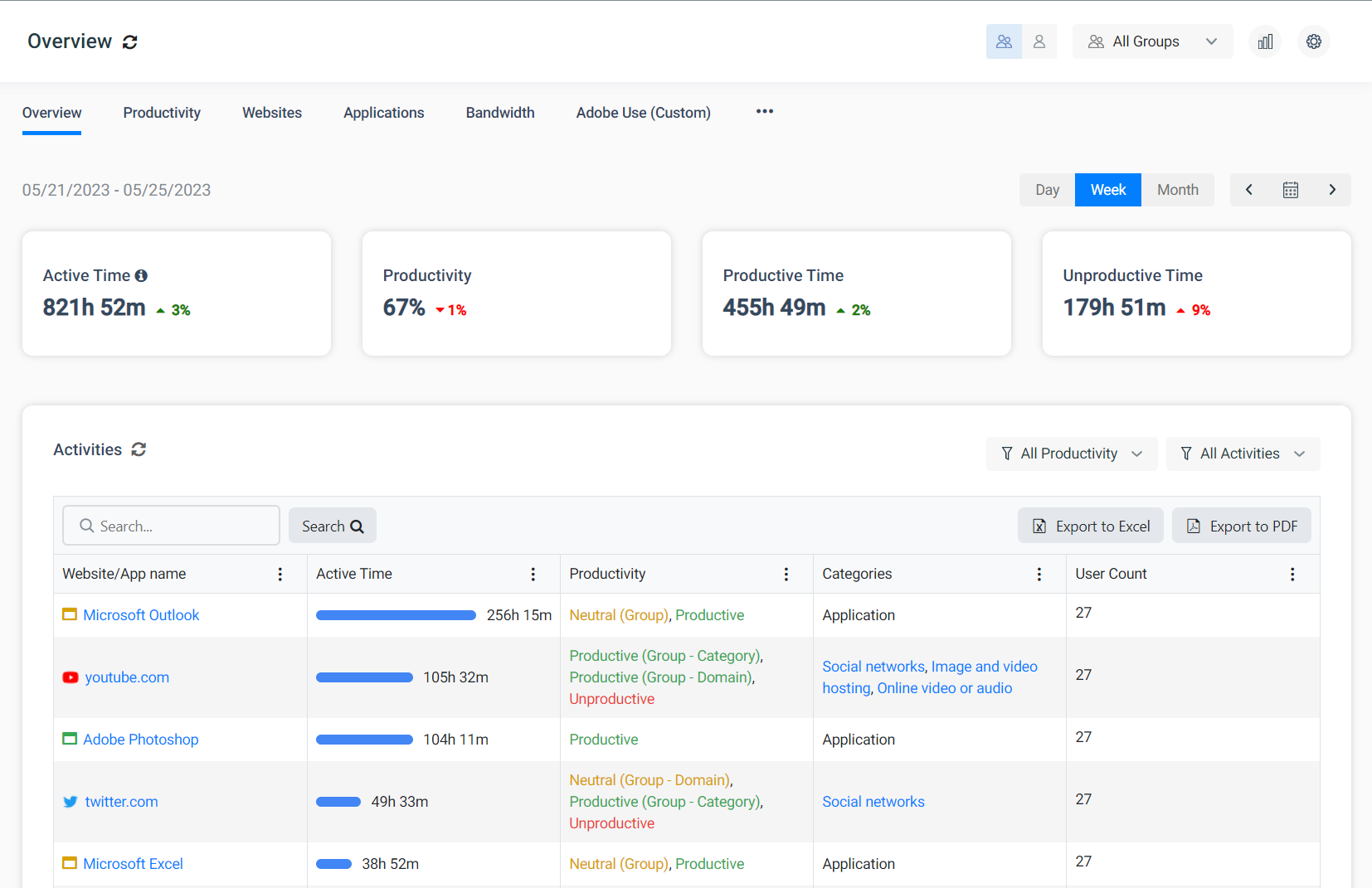
Citrix End-User Productivity Reporting
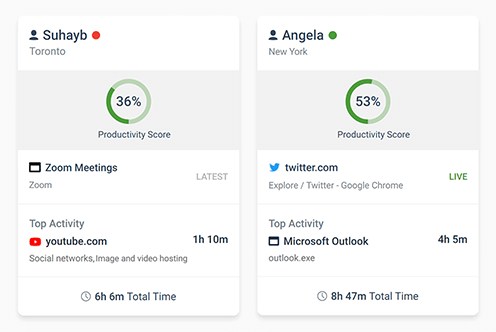
Using BrowseReporter’s user activity reports you can monitor the Citrix activity levels of your employees to track their productivity.
BrowseReporter also audits the internet and application usage of users that connect to remote computers using remote desktop and similar technologies.
If you have employees who work from home you can use the end-user activity reports to verify that they were using their computers during work hours.
BrowseReporter even includes a pre-built employee productivity report that provides a high-level overview of how much time your employees spend on websites that are productive, unproductive, or neutral. These classifications can be customized to match what is considered productive for your employees.
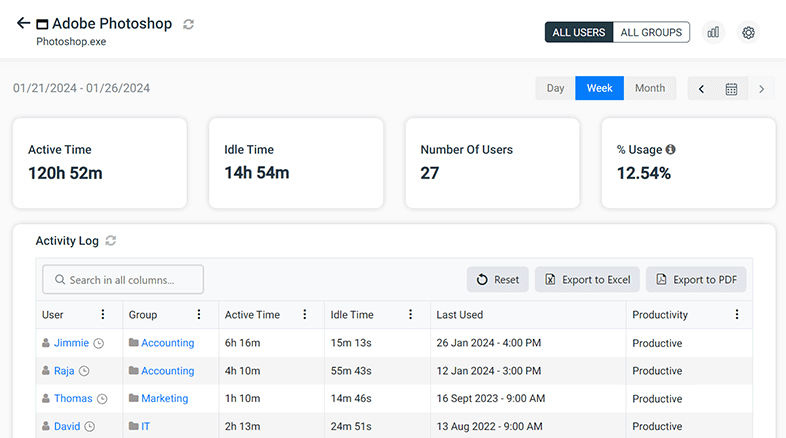
Monitor Internet and Application Usage on Citrix
Monitoring internet and application usage is essential for ensuring that your remote users are in compliance with your company’s acceptable use policies.
When your employees browse the internet or use applications on a Citrix virtual desktop, their activity data will be collected by the CurrentWare client.
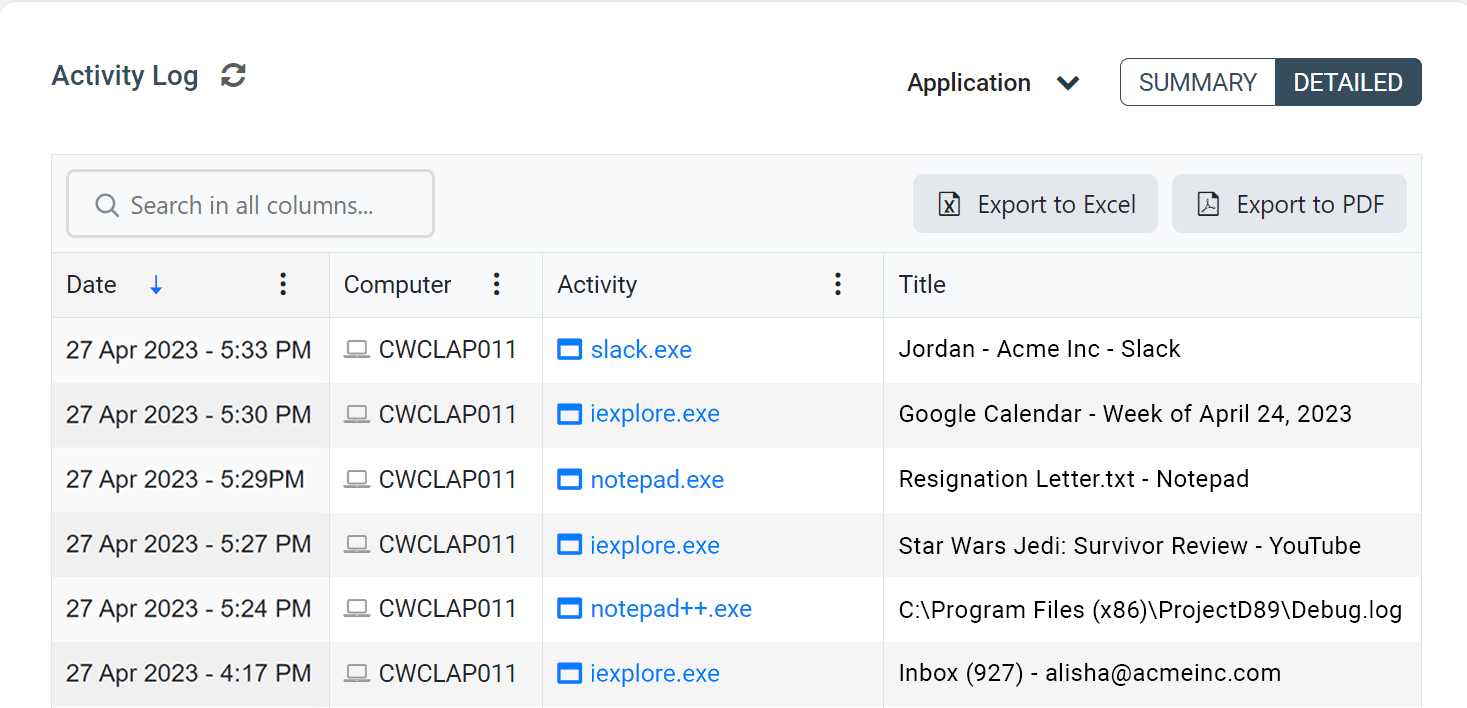
Samples of BrowseReporter’s internet and application activity reports
Take Screenshots & Remote View Citrix Virtual Desktops
Monitor employee desktops in real-time with the remote screen capture feature. Get a live feed of what an employee is doing on their computer and remotely capture screenshots of their desktop.
- Remotely take screenshots of other computers in your network, even on dual-screen setups
- Monitor desktops in real-time to watch for unsafe data handling and inappropriate behavior
- Capture screenshots at particular intervals for specific users/computers or based on triggered events
Track End-User Active vs Idle Time on Citrix
BrowseReporter measures the Idle Time of your users to see how long they are away from their workstation. Using the email alerts feature you can even get notified when a user is idle for a predetermined period of time.
The distinction between Active Time and Idle Time is based on their mouse and keyboard activity. When there is no input from their mouse or keyboard for a designated period of time, BrowseReporter will shift tracking from Active Time to Idle Time.
By default, the amount of time that the end-user must be inactive before BrowseReporter switches from Active Time to Idle Time is 20 minutes. This threshold can be customized to better suit your environment.
BrowseReporter’s integrated system idle time tracker sorts remote user activity into three categories based on their usage:
- Active Time is how long the employee was actively using their computer. A computer is considered active when mouse and keyboard inputs are detected.
- Idle Time is how long a given website was left open but was not actively being used.
- Total Time is the full length of time that a given website was open (active time + idle time)
Learn More: Track the Idle Time of Employees
Audit File Transfers to Portable Storage Devices on Citrix
With AccessPatrol’s device control features you can prevent data exfiltration when employees work from home.
With the CurrentWare Client installed on the devices you would like to monitor you can detect when USB devices are plugged in to domain controllers, servers, Citrix VMs, and other Windows-based endpoints.
You can also configure alerts that notify you when files are transferred to portable storage devices or when certain peripheral devices are inserted into monitored endpoints.
Sample USB Device Reports
File Operations
Allowed vs Denied USB Devices History
Bonus: Block Websites & Portable Storage Devices on Citrix
In addition to tracking user activity Citrix, the CurrentWare Suite includes:
- BrowseControl content filtering software for blocking websites, applications, and network ports.
- AccessPatrol device control software for monitoring and restricting peripherals such as USB flash drives, external hard drives, and network share drives.
These tools further enhance the security of your Citrix environment by providing you with the means to protect against data theft and the use of high-risk/inappropriate websites.
When applying web filtering and/or device control policies in Citrix with CurrentWare you can apply policies with PC Mode to control the individual virtual machine or with User Mode to control the permissions of specific employees across multiple devices and/or virtual machines.
How CurrentWare’s Software for Tracking User Activity in Citrix Works
CurrentWare’s Citrix user activity logging software is supported on desktop computers, virtual machines (VMs) and servers running the Windows operating system.
In addition, all CurrentWare components are compatible with Remote Desktop Services (RDS) or Terminal Servers (TS).
So long as the underlying operating system is a version of Windows that is supported by CurrentWare, your users can be monitored.
This means that you can audit user activity on Desktop as a Service (DaaS) providers such as Amazon Workspaces and Citrix, self-hosted Virtual Desktop Infrastructure (VDI), or physical endpoints that are being accessed through remote desktop, DirectAccess, or a VPN.
CurrentWare is known to be compatible with the following virtualization software:
- VMware
- Parallels
- VirtualBox
- Oracle VM
- Virtual-PC
- Hyper-V
CurrentWare integrates with Active Directory, allowing you to import your Windows users and OUs directly from your Active Directory onto the CurrentWare Console.
CurrentWare allows you to set custom data grooming/data retention periods, allowing you to keep records of end-user activities on Citrix virtual desktops for as long as your organization needs.
When monitoring and managing your end-users in Citrix with CurrentWare you can track and control computer activities with PC Mode to manage the individual virtual machine or with User Mode to track and control the activities of specific users across multiple devices and/or virtual machines.
Monitoring and managing your end-users with CurrentWare in a Terminal Services environment works similarly. The exception is that in a Terminal Server/Terminal Services environment, the server will be registered as an individual endpoint; when you run a report from PC mode it will give you a report on all the users’ profiles in a single report.
Remote Monitoring Software Agent
CurrentWare tracks user activity in Citrix with a software agent that is installed on each endpoint (virtual or physical) that you would like to monitor. The CurrentWare client agent is responsible for receiving the policies from your CurrentWare Server and triggering them locally on the remote computer.
The CurrentWare Client agent is able to differentiate between each user that is logged in. This allows you to separate your users/endpoints into logical groupings and apply unique security policies to them or run reports on their individual computer activities.
- Integrity: The user activity monitoring software offered by CurrentWare is protected from attempts to stop or uninstall the agent by the end-user.
- Connectivity: Even if the connection between the CurrentWare Server and CurrentWare Client is lost, the CurrentWare Client will continue to monitor your employees. The user activity data and last known security policies will be stored locally until a connection to the CurrentWare server is re-established.
- Visibility: The CurrentWare Client can be deployed in stealth mode or with optional privacy-enhancing features enabled.
Tracking User Activity in Citrix vs Monitoring Local Endpoints
How you will deploy CurrentWare to start tracking user activity in Citrix depends entirely on the needs of your environment.
If you would like assistance with your CurrentWare deployment or evaluation our technical support team is available to assist you over the phone, live chat, or email.
If you would like to monitor Citrix virtual desktops, you will install the CurrentWare client on the Windows Server that is hosted on Citrix.
If you would like to remotely monitor the end-user’s physical endpoint, you will need to install the CurrentWare Client on their computer.
To reduce potential privacy concerns the best practice is to provide your remote users with a company-owned device and have them sign a written policy that alerts them to the nature of the monitoring.
Workplace Monitoring Policy Template
- Disclose your company’s intent to monitor employees in the workplace
- Set workplace privacy expectations for employees
- Meet transparency requirements for compliance with privacy laws
Get started today—Download the FREE template and customize it to fit the needs of your organization.
For more information on workplace privacy and employee monitoring, download our free white paper.
Does Citrix Track Activity?
Citrix comes with an excellent suite of monitoring tools for tracking end-user experience, detecting potential security risks, and diagnosing the health status of Citrix virtual apps and desktops.
But when it comes to monitoring the productivity of remote workers, integrating Citrix with CurrentWare’s user activity monitoring software will produce the best results.
By integrating CurrentWare with Citrix you can track granular details about the websites that employees visit, how much time they spend browsing the web, and the time they spend on productive vs unproductive websites.
What User Activity Does Citrix Log?
In terms of tracking user activity in Citrix, there are some native options.
While the names and functions of these monitoring tools have changed over the years (SmartAuditor, Citrix Analytics, Citrix Director, etc), Citrix’s focus has been on tracking performance metrics related to the health of the Citrix platform rather than the specific activities of end-users.
Citrix’s monitoring tools help diagnose end-user experience issues by tracking things like…
- Session failures
- Logon duration times
- VDA registration failures
- Bandwidth usage
- Domains accessed
- Etc
For example, consider this excerpt about the Performance Analytics service from Citrix Analytics:
- Performance Analytics aggregates Site performance metrics into easy-to-view User Experience and Infrastructure dashboards. They help you analyze the user experience and optimize the usage of your Citrix Virtual Apps and Desktops Sites.
- Performance Analytics quantifies the user performance factors and classifies the users based on these factors. It provides actionable insights to troubleshoot failures, screen lags, delayed session logons, and other performance indicators.
- Performance Analytics allows you to find and filter metrics to narrow down to specific users or sessions facing performance issues.
Source: Citrix Product Documentation, January 2021
Citrix Security Monitoring
That said, over time Citrix has introduced some monitoring tools that log user activity for security and compliance purposes.
For example, the Platinum Edition of Citrix XenApp and XenDesktop (which has since been rebranded to Citrix Virtual Apps and Desktops) introduced Session Recording, a feature that allows administrators to record and playback user sessions.
Here’s Citrix’s summary of the Session Recording feature:
“Session Recording is a key component in Citrix XenApp and XenDesktop Platinum Edition that enables IT admins to record active virtual apps and desktop sessions, based on user, application or server and then save the recording file for future reference when needed.”
Along the same vein, they have also introduced web security monitoring in Citrix Secure Workspace Access.
This monitors things like…
- The number of hits to websites that are malicious, dangerous, or blocked
- Which users visit risky websites the most
- Data download volume from risky sites
These are certainly valuable features for industries that need to protect sensitive information in a remote environment, but it lacks the granularity needed to monitor the productivity of remote employees in a Citrix environment.
Since they are primarily used for network performance monitoring, the data that is accessible through Citrix’s internet usage reports also suffer from “noisy” data—content delivery networks, advertisements, etc. BrowseReporter’s reports filter out this data for you so you can focus on what the end-user was actually doing.
Key Takeaway
When it comes to logging user activity for productivity management purposes, CurrentWare’s end-user productivity monitoring tools for Citrix give you the granular insights you need to track what each individual user was doing.
Start Tracking User Activity in Citrix With CurrentWare
CurrentWare’s end-user productivity reports for Citrix audits user activity on local or cloud based desktop computers, virtual machines (VMs) and servers running the Windows operating system.
In addition, all CurrentWare components are compatible with Remote Desktop Services (RDS) or Terminal Servers (TS).
The CurrentWare Suite provides dozens of remote desktop activity reports for auditing how end-users interact with endpoint devices.
These reports include…
- User logon session duration
- Internet activity reports (search queries, bandwidth consumption, sites visited, browsing time, etc)
- Application usage reports
- Active vs idle time tracking
- USB activity reports (files copied/created/deleted/renamed to portable storage, peripheral devices used, etc)
Many of these reports can be configured as email alerts to notify you when specific actions occur on monitored endpoints.
In addition to Citrix user activity reports, the CurrentWare Suite includes solutions for peripheral device control, web content filtering (without the need for SSL inspection), and remote power management.
Learn More