How to Monitor Employee Computer Activity (& Why You Should)

Watch this video to learn how to monitor employees working from home using a free trial of BrowseReporter, CurrentWare’s remote employee monitoring software.
Ready to get started right away? Download a free 14-day trial of our remote employee monitoring software solutions; no credit card required!
Our team is here to help you. We will help you get set up and provide ongoing support during your time as a CurrentWare customer.
What Is Employee Computer Monitoring Software?
Employee monitoring software is a program that enables employers to gather valuable data about their employees’ activities.
Whether in an office-based, remote, or hybrid workplace, an employee monitoring tool allows employers to track employee activity, such as:
- The websites and applications employees use
- The amount of time they spend on different tasks
- File uploads, downloads, and transfers
- How active they are on their computers
These tools provide valuable insights for employers, helping them optimize workforce productivity and make data-driven decisions
What Type of Employee Activity Can be Monitored?
- Web Browsing: Employers can monitor the websites employees visit to analyze productivity and identify potential distractions.
- Application Usage: Employers can track which applications employees use and how frequently. This provides insights into software utilization rates and the use of unauthorized software
- Track Employee Productivity: The best employee monitoring software will include productivity monitoring features that allow you to measure productivity based on how much time employees spend on websites and apps that are considered unproductive.
- File Transfers: Monitoring file transfers to cloud storage services and external storage drives helps detect unauthorized data sharing attempts
- Email Communication: Monitoring employee email activity allows employers to track inbound and outbound work emails. It helps prevent data leaks and ensures compliance with company policies.
- Keystroke Logging: Keyloggers record every interaction a user has with their keyboard; since this includes passwords and sensitive messages, keystroke logging tools are seldom used.
- Desktop Screenshots: Get a live feed of an employee’s computer screen and remotely capture screenshots of their desktops
- Automated Time Tracking: Monitoring work hours, breaks, and time spent on specific tasks helps optimize productivity and manage workloads. It may also assist with task management by assigning employee activity to a specific task.
- Location Tracking: For field or remote workers, location monitoring ensures they are where they should be during work hours.
How to Monitor Your Employees’ Computer Activity
How to Install Employee PC Monitoring Software
- Sign up for a free trial to get the installation files for CurrentWare’s employee monitoring tool
- Following these installation instructions, install the CurrentWare Console on a manager’s computer and deploy the CurrentWare Clients on employee computers
- You are now monitoring employee computer activity. From the CurrentWare Console, you can use BrowseReporter to generate detailed reports of employee computer activity.
Want to use CurrentWare to monitor remote employees? Follow this tutorial
How to Monitor Computer Activity While Respecting Employee Privacy
In today’s privacy-conscious world employers need to monitor employee computers in a way that is transparent, minimally invasive, and respectful of employee privacy.
When you track employee activity it is essential to establish clear privacy expectations, treat employee activity data the same way you would treat any other confidential data, and be mindful of your legal compliance obligations based on collective bargaining agreements and workplace privacy laws in each jurisdiction you will be tracking employee activity.
Most employee monitoring software will provide you with the option to conduct employee surveillance either stealthily or transparently. While in many jurisdictions (particularly in the United States) employers are permitted to monitor company computers for legitimate business purposes, it’s critical that you consult with legal counsel to verify your responsibilities and monitoring limitations as an employer.
To help you track employee computer activity in a lawful and reasonable manner, the CurrentWare team has prepared a variety of critical resources related to the best practices when using employee monitoring systems.
Workplace Privacy & Employee Monitoring Resources
- CurrentWare’s Privacy-Focused Features
- White Paper—The Best Practices for Monitoring Employees
- Employee Monitoring Starter Kit
- Workplace Monitoring Policy Template
- Privacy Tips for Monitoring Employees in the Workplace
How to Introduce Employee Monitoring Software to Your Team
Introducing employee monitoring software to your team can be a delicate process. Here are some practical steps to ensure a smooth transition and minimize any negative reactions:
- Transparency is Key:
- Inform your team openly about the decision to implement monitoring software. Ensure that someone is available to note any concerns and act as an advocate for employees during the initial planning stages.
- Focus on work-related activities: Clearly define what will be monitored and the purposes of the data collection. Emphasize that the software is intended to track work-related tasks and objectives, such as software utilization and to ensure nobody is visiting high-risk or inappropriate websites.
- Personal privacy: If employees worry about personal information being captured by monitoring tools, ensure that your company clearly states that company devices are for work purposes only and only install computer monitoring software on devices that employees will not use for personal reasons.
- Effective Communication:
- Engage in open dialogue: Discuss the reasons behind implementing monitoring tools with your team.
- Answer questions: Be prepared to address concerns. Explain the purpose of monitoring and how it benefits both the company and employees.
- Build Trust:
- Maintain transparency: Regularly communicate about the monitoring system. Reassure employees that productivity tracking and time tracking will be used to improve business intelligence rather than as a punitive measure.
- Avoid secrecy: Discreetly installing monitoring software will erode trust. Employees who discover they are being secretly monitored by employee tracking software are more likely to assume nefarious intentions from their employer.
- Involve Employees:
- Include them in the process: Seek feedback and involve employees in discussions. Their input can help shape your monitoring policies and proactively address concerns with an honest dialogue.
Remember, the goal is to strike a balance between productivity and respecting individual privacy. By being transparent and using the data fairly you can successfully introduce employee monitoring software without causing unrest within your team.
Learn More: How to Get Buy-In for Employee Tracking Software
Employee Computer Activity Monitoring Software Buyer’s Guide
Deciding on what the best employee monitoring software solution is for an organization can be a daunting process as individual requirements will change depending on its infrastructure, the types of monitoring they would like to conduct, their data privacy and security compliance requirements, as well as several other factors.
This employee monitoring software buyer’s guide covers the essential considerations your organization must evaluate when determining the best employee monitoring software for its needs.
Define Your Goals
In order to get the most value out of employee monitoring tools, your organization must have a clear understanding of the goals it has and how its employee activity monitoring strategy will best meet those goals.
For example, employee monitoring software provides insights into employee web browsing habits. This data is essential for ensuring that all employees are following your organization’s acceptable use policies.
Common Goals Include:
- Ensuring compliance with data privacy and security regulations
- Monitoring employee behavior to mitigate and detect insider threats
- Prevent the inappropriate usage of the internet and bandwidth
- Improving employee productivity
- Enforcing acceptable use policies for technology in the workplace
Key Features of the Best Employee Monitoring Software & Vendors
The best monitoring software records a variety of computer activities, including:
- Internet history (Websites visited, idle/active time, etc)
- Applications used
- Bandwidth usage
- File operations (files that are copied/created/deleted)
- Startup/shutdown events
- Logon/logoff events
These tools can also send email notifications to alert a manager when undesirable or suspicious activities happen on monitored computers. These detailed reports serve as valuable evidence of unproductive or high-risk computer activity.
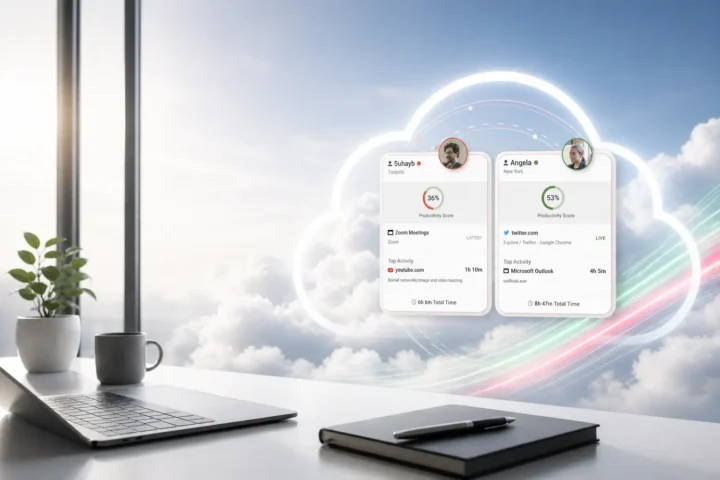
Real-Time Activity
It’s important to keep a pulse on your team’s real-time activity to ensure everyone is online and working as expected. With an at-a-glance overview of metrics such as their online status, most recent app/website, and top activities you can get a convenient high-level view of employee productivity.
Internet Use Monitoring
One of the most common uses of employee activity monitoring software is website tracking. Insights into bandwidth consumption, web browsing, and search queries provide detailed evidence of web activity, making it the perfect tool for enforcing internet use policies.
Software Utilization
36% of desktop software & 29% of SaaS spend is underutilized or wasted, with the average cost of unused computer software being $259 per desktop.
In this economic climate organizations need to maximize the value of their software investments by reducing unnecessary expenses and ensuring productivity-enhancing tools are adequately adopted.
With insights into software utilization organizations can optimize software spend by identifying opportunities to reduce licenses for underutilized software and consolidate licenses for redundant solutions.
Track Employee Productivity
How much time is spent using productive vs unproductive applications and websites? Employee productivity insights equip managers with the activity data they need to understand how employees are spending their time at work, whether you have in-office or remote employees.
Screenshot Monitoring
Automatically capture screenshots of employee desktops when specific websites or applications are used, or take screenshots at a set interval. Screenshot monitoring provides a visual record of employee activities to complement other activity data such as productivity tracking and employee time tracking.
Idle vs Active Time & Logon/Logoff Times
Time tracking with employee monitoring tools can provide incredibly valuable insights, but only if the productivity reports are truly accurate.
To get the most accurate and detailed reports, you need to monitor employee activity in a way that differentiates between what the employee is actually spending time on vs what is simply open on their computer.
With idle time tracking, keyboard and mouse usage are tracked to determine if an employee is actively using their computer. After a predetermined period of inactivity, the employee monitoring tool will consider the user idle.
Logon tracking helps verify employee attendance, detect computer activity outside of normal working hours, and provide insights into when employees with flexible schedules are typically working.
Dedicated Account Managers & Support Staff
Since monitoring tools need to integrate with increasingly complex systems it is critical that the vendor allows its customers to contact customer support for technical issues. When deciding on a software vendor, look for one that has telephone-based support during hours that your business is typically open.
Custom Data Retention Settings
Organizations that have a legal requirement to use employee monitoring software need to ensure that the data is accessible for review.
Employee monitoring software with configurable data retention settings makes auditing, compliance, and storage less of a hassle for large-scale deployments. The ideal employee monitoring software will allow the organization to store the data indefinitely to ensure that records are maintained as long as needed or have the activity logs periodically purged.
Automated purging saves organizations considerable costs on storage and administration as they will not need to manually purge the data, purchase new storage hardware, or upgrade to a greater storage volume with their cloud storage provider.
This automated culling is especially important for any business that is subject to data privacy legislation. These regulations typically require that employee information is only kept for as long as it is relevant and necessary for the company.
Administrative Permissions & Groupings
User grouping features such as Organizational Units (OUs) within Active Directory allow administrators to efficiently implement and adjust bespoke settings based on department, location, user, the types of information handled, and other important considerations.
Bespoke settings ensure that the solution does not cause a bottleneck in productivity. Inflexible employee monitoring software will cause less at-risk users to have the same policy restrictions and monitoring policies as users who perform tasks with sensitive information such as personal health information (PHI).
For large enterprises and other expanding organizations, the ability to group users and devices based on location, department or role is crucial to limit the time investment required in managing the monitoring solution.
Best-in-class enterprise computer monitoring software solutions allow for granular control of the product’s features including who can run reports, who has access to a given group’s reports, and who will receive automated email reports based on the activity of the designated groups.
Real-Time Alerts & Notifications
Real-time alerts and other notifications are critical components of insider threat detection as they can be configured to alert administrators to insider threats engaging in suspicious or risky behavior.
Real time alerts can include:
- File Operations Alerts: Alerts when an attempt is made to copy files to an unauthorized external storage, when sensitive file types are being accessed, or other suspicious file operations. This is especially useful for preventing breaches caused by malicious insider threats.
- Inappropriate Website Use: An employee attempts to access websites that are considered not safe for work (NSFW) in the organization.
- Browsing/Bandwidth Limit Reached: An alert can be sent to users when they have exceeded their allotted browsing time or bandwidth usage for the day.
The Pros and Cons of Employee Monitoring
Note: The above video showcases a legacy user interface for BrowseReporter. To see the most up-to-date features and interface please visit the BrowseReporter product page
“Employers that don’t monitor [their employees] will become fewer and fewer, not to nail employees, but because monitoring increasingly makes business sense.”
Manny Avramidis, president and CEO, the American Management Association
Pros of Monitoring Employee Computer Activity
Improve Employee Productivity
With user activity insights you can see who is working diligently, who may be overworked, and who is simply pretending to work. Use these insights to make data-informed management decisions and ensure everyone is on the same page.
- Who hasn’t logged in yet today?
- Who has stepped away from their computer?
- Who is actively working at their computer?
- What activities have my team members spent most of their time on?
- How long have they been working on their computers today?
- What are the average productivity levels of each team?
- How does location flexibility affect employee engagement?
- What unproductive applications and websites are excessively distracting my team members?
These insights are especially valuable for remote workforce management as it proactively addresses the visibility gaps associated with them.
Monitoring Software Limits Distractions
Cyberloafing – also known as cyberslacking – is a term that’s used to describe employees engaging in technology distractions in the workplace such as browsing the web in ways that aren’t related to work.
While a small amount of cyberloafing can help blow off some steam between projects, excessive non-work web browsing can turn a stint of cyberloafing into full-on time theft.
The key is to strike a balance between non-work internet use and the employer’s need for their employees to be productive in the workplace. Generally employees are given the opportunity to manage their own productivity and they are trusted to use the internet appropriately, however in some cases the internet becomes a serious productivity block.
Remote employees who know that their performance and computer usage are being monitored will be more focused on their core tasks and less tempted to become distracted by time sinks such as social media, internet forums, and shopping websites.
Monitoring Software Identifies Shirkers
The insights provided by time tracking and productivity monitoring tools help improve productivity in a variety of ways.
For example, monitoring employee work performance helps to identify actively disengaged employees who are engaging in time theft by misrepresenting their efforts. This level of visibility is especially important when managing remote workers as they are trusted to perform their best with minimal supervision.
Without computer activity reporting features to provide clear evidence of activity an unscrupulous employee could claim they were working as expected, all the while being engaged in non-work activities.
On the opposite side of this, remote employee productivity reports are an excellent way to find out which of your remote workers are the most productive and engaged. This allows you to reward and encourage productive employees that may otherwise have gone unnoticed.
Detect & Deter Time Theft
At its core, time theft occurs when an employee accepts payment for work or time they did not actually complete. Time theft comes in a range of degrees of severity, from employees mismanaging their allocated break times all the way up to intentionally fraudulent claims.
Examples of Time Theft
- Taking extended lunch breaks without permission.
- “Buddy Punching” – Convincing coworkers to punch in on their behalf when they aren’t present for work.
- Exaggerating how much time was spent working on tasks or their overall amount of work hours.
- Spending excessive amounts of time on non-work tasks (“Cyberloafing”, excessive socializing, sleeping, playing games, working on personal projects)
- Working unauthorized overtime and sneakily extending their billable hours to maximize their paycheque
Monitoring employee activity improves the accuracy of employee time tracking by verifying that employees are active on their work devices.
Some employee tracking solutions even include dedicated time tracking features such as punch clocks and the ability to assign periods of time to a specific project and task. This helps assist project management by estimating project costs, ensuring that optimal project and task focus is achieved, and assisting with task tracking.
Moreover, enterprise project management software can further streamline these processes by providing a centralized platform for time tracking, resource allocation, and project budgeting, and offering real-time insights into project health.
Hybrid/Remote Team Management
Managers of remote and hybrid teams often struggle to keep a pulse on their team’s productivity and availability. With the best employee monitoring software you’ll get detailed productivity reports that provide details about what applications or websites are currently in use, online statuses, top activities, and who hasn’t started working today.
Insider Threat Detection & Data Loss Prevention
Data breaches can have a devastating impact on companies, causing a ripple effect of financial losses, reputational damage, and legal consequences. Here’s a breakdown of some key areas affected:
Financial Losses:
- Direct Costs: Companies incur significant expenses to investigate the breach, contain the damage, notify customers, and improve security measures. This includes costs for forensic analysis, legal fees, credit monitoring services for customers, and potential ransom payments.
- Lost Revenue: Breaches can lead to a decline in sales as customers lose trust and take their business elsewhere. Companies may also be forced to raise prices to cover the costs associated with the breach.
- Decreased Productivity: Data breach events disrupt normal business operations as IT teams scramble to contain the breach and restore systems. This can lead to lost productivity and decreased efficiency.
Reputational Damage:
- Loss of Trust: When a company experiences a breach, it can severely damage its reputation and erode customer trust. Customers may be hesitant to do business with a company they perceive as insecure.
- Negative Publicity: Data breaches often make headlines, leading to negative publicity that can further damage a company’s reputation. Social media can amplify the negative impact, making it difficult to control the narrative.
Legal and Regulatory Issues:
- Fines and Penalties: Many countries have data protection regulations that mandate companies to secure customer data. Companies that fail to adequately protect data may face hefty fines and penalties.
- Lawsuits: Customers affected by a breach may file lawsuits against the company, alleging negligence or a failure to protect their personal information.
The overall impact of a breach can be significant, potentially leading to a company’s financial ruin or even collapse.
User Activity Monitoring (UAM) helps identify suspicious behavior by monitoring end user actions on devices, networks, and company-owned resources.
Monitoring employee activities provides an early warning system of malicious and negligent insider threats, such as attempts to transfer sensitive information to portable storage devices, anomalous login/logout times, visits to high-risk websites, and the downloading of suspicious files.
Monitoring how trusted employees interact with company data is an essential part of any DLP strategy. Monitoring tools are instrumental in preventing security breaches by providing insights into the activities of employees with sensitive data access privileges.
For example, if an employee attempts to transfer sensitive data such as employee files to an external hard drive, monitoring software can alert security teams of the attempted data breach so they can take action and confront the employee.
How employee monitoring improves security
- Interactions with sensitive information can be monitored to ensure compliance with security policies
- Monitoring internet use can detect attempts to visit unauthorized cloud storage sites
- Application usage can be monitored for potentially dangerous unauthorized applications such as shadow IT and pirated software
- Intellectual property and other sensitive information can be closely monitored during the offboarding process to prevent theft
- Unusual outbound network traffic is one of many potential indicators of compromise (IOCs). Monitoring user activity for anomalous bandwidth spikes, and visits to unauthorized cloud storage sites are all potential warning signs
Case Study
Viking Yachts Stops an Employee From Stealing Their Intellectual Property
As Viking Yachts grew, their network administrator Vincent Pecoreno was responsible for supporting over 530 users and 1500 devices across multiple geographic locations, making visibility a challenge without the right tools in place.
Once equipped with CurrentWare’s user activity monitoring and data loss prevention solutions, Viking Yachts had the insights they needed to protect their sensitive data.
Read their case study to learn more about how Vincent used CurrentWare to detect a data theft attempt from a soon-to-be-ex-employee.
Enforce Company Policies
Employers need to ensure that their employees are behaving in an appropriate and professional manner. Allowing employees to engage in unsavory actions on company-owned computers is a significant contributor to a hostile work environment.
Having a formal computer use policy is an essential first step for communicating expectations to employees, but it’s not the full solution. Employee tracking software is a valuable tool for enforcing policies as it can alert HR and management to computer policy violations such as visits to adult-oriented sites.
How employee monitoring helps enforce policies
- Identify employees who are visiting inappropriate or unsafe websites
- Evidence of misuse can be kept on file to support a performance improvement plan
- Employee internet monitoring software can be used in tandem with a web filter to ensure that employees are not going to sites that are not suitable for a work environment
Improve Bandwidth Availability
By monitoring employee bandwidth consumption you can identify unproductive bandwidth hogs that affect network performance such as streaming sites. In a shared network these bandwidth hogs negatively affect the performance of the entire network, and thus harm employee productivity across the board.
To address this concern you can monitor computer usage, identify bandwidth abuse, and use a web filter to prevent unauthorized access to these sites. While network monitoring tools will provide insights into high-level bandwidth utilization, a client-based monitoring tool will provide more specific details of the usage from a specific computer.
Cons of Monitoring Employee Computer Activity
The greatest cons of employee monitoring relate to the potential impacts on privacy, workplace culture, and morale.
As the spectrum of what is considered “employee monitoring” varies widely, the cons of monitoring will vary depending on employee perceptions, who has access to their information, the invasiveness of the chosen monitoring methods, and how the information is used.
When monitoring your employees you should consider both the pros and cons of the monitoring tools you intend to use.
Employee Monitoring vs Workplace Privacy
In today’s privacy-conscious world employers need to monitor employees in a way that is transparent, minimally invasive, and respectful of employee privacy and autonomy.
They need to carefully balance the demands of organizational productivity, privacy, and regulatory compliance requirements surrounding the storage, use, and protection of their employee’s data.
One of the cons of employee monitoring software is that potentially sensitive personal information may be captured. If employees doubt whether or not their personal information is adequately protected from misuse there is a legitimate concern that their web browsing history can be unfairly used against them.
Before you monitor your employees you must have them sign an employee monitoring policy that outlines what will be captured, who will have access to it, and how the data of workers will be used.
The most common employee privacy concerns
- If employees use their work computer for personal tasks the monitoring software may capture personal details such as racial identity, personal web browsing habits, religious beliefs, and health concerns
- Automated screenshot capturing software will capture everything on their screens including banking details, personal messages they may be writing, and any classified information they may be working with
- Employees could be concerned that the insights will be used unfairly or that their activity data will create a bias that will impact their professional career
Invasive Monitoring May Lead to Legal Issues
When monitoring employees in the workplace you must comply with any laws or regulations that pertain to an employee’s privacy rights in the workplace.
When it comes to what you are allowed to monitor, many believe that if an employee is using company equipment, on company time, and getting paid by the company, that the company has every right to monitor their equipment and what the employee is doing with it.
While in the majority of cases a company can monitor their employees so long as they have a legitimate business reason for doing so, it’s not always that simple. A variety of factors influence what employers can and cannot monitor.
For example, keystroke logging software is an invasive form of employee monitoring that can potentially capture personal data such as passwords. Even with a policy in place an employer may not have the legal right to use keystroke logging and other needlessly invasive tools.
Legal factors that influence an employer’s right to monitor
- Jurisdiction: Employee monitoring laws vary depending on where the employer and the employee reside. A catch-all approach may not be suitable for a multinational company.
- Union Agreements: Independent agreements with unions and other workers’ rights organizations may include limitations about what employers can track and how data will be used when monitoring employees.
- Proportionality: Different forms of monitoring may be restricted based on potential privacy impacts. For example monitoring individual keystrokes is more invasive than monitoring web browsing history as tracking specific keystrokes has a greater chance of capturing sensitive personal information such as passwords.
- Privacy Expectations: Employees have a greater expectation of privacy on their personal devices. Monitoring laws may even go so far as to restrict the degree of monitoring that can take place when employees use business equipment for personal use.
- Transparency: Has the company made a legitimate effort to inform employees that they are being monitored? Are employees clear about whether or not they have a reasonable expectation of privacy on workplace equipment?
H&M Fined Millions Under GDPR for Invasive Monitoring
In 2020 the clothing store H&M received a €35.3m ($41.3m USD) fine for invasive employee monitoring practices.
H&M received the fine due to non-compliance with the General Data Protection Regulation (GDPR), a data protection and privacy legislation that protects data subjects in the European Union (EU) and the European Economic Area (EEA).
Why was H&M’s monitoring considered invasive?
Managers at H&M collected sensitive personal information through extensive employee surveys and even notes from informal conversations.
The data included how staff conducted their holidays, medical symptoms, diagnoses for illnesses, family issues, and personal religious beliefs. That data was then made available to up to 50 managers who used that data to make employment-related decisions.
Since this collection was excessively invasive and collected information that was beyond any legitimate business need, the Data Protection Authority of Hamburg (HmbBfDI) opted to issue the fine.
Potential Impacts on Employee Morale
“Employers must not use tech to control and micromanage their staff. Monitoring toilet breaks, tracking, and snooping on staff outside working hours creates fear and distrust. And it undermines morale.”
Frances O’Grady, General Secretary of the British Trades Union Congress (As reported by Raconteur)
Another con of employee monitoring is that some forms of monitoring can have a negative impact on employee morale. Employee perceptions of monitoring may also contribute to added stress that affects work performance.
Providing employees with autonomy is essential for maintaining morale. If employee monitoring is used to micromanage employees and punish them for minor infractions they will feel like they are being unfairly treated.
When using employee monitoring software it’s important to avoid reducing human employees to mere numbers. Workforce analytics tools are excellent at capturing quantitative data, but they cannot reliably track qualitative data.
Even if that is not the intention of the employer, a lack of communication and transparency can cause these sentiments to form. Not all employees will be willing to give the benefit of the doubt if they discover their employee was secretly using employee tracking software.
That’s why it is critical that the deployment of employee monitoring software is done with the input of a representative sample of employees. Involving employees in the planning process gives business leaders the opportunity to proactively address any privacy or management concerns before any monitoring takes place.
Employers must also do all they can to clearly communicate their intended use of employee data, especially if that data will be used to make any sort of judgment on employee performance.
How employee monitoring software can harm employee morale
- Lost Autonomy: Employees may feel that their workflows will be unfairly micromanaged based on their computer activity data and other quantitative metrics.
- Distrust: Employees may assume that their employers are monitoring their activity because they are not trusted to act professionally and manage their own productivity.
- Stress: Employees may feel that they are at risk of being fired or otherwise unfairly evaluated based on the data collected.
- Evaluations: Computer activity data is not a reliable standalone worker productivity metric. Employees who are not fairly evaluated with other relevant metrics will grow to detest their employer’s monitoring practices.
Misuse or Breach of Sensitive Employee Data
Many data privacy laws require that data collection is performed for a specific purpose. This is a preventative measure to ensure that the informed consent provided by the data subjects (the employees) is respected during collection, processing, and use.
A successful employee monitoring strategy requires a clear understanding of the company’s goals and how the data collected will be used to meet them. If employee data is collected under one stated purpose and used for another it can lead to data privacy compliance violations and severe impacts on employee morale.
Employee monitoring data must also be treated as sensitive and protected accordingly. This includes limiting who can access the data, restricting the use of the data to its intended purpose, and implementing necessary safeguards.
The risk that an employee’s data could be leaked to an unauthorized third party may contribute to an employee’s hesitation to be monitored in the workplace.
The risks of misuse or breach of employee data
- Blackmail/Gossip: An employee’s internet search history can potentially contain private details about their personal lives. Without administrative controls in place this data can be leaked to their coworkers or other parties.
- Trust & Retention: If employees cannot trust that their data is adequately secured they may feel unsafe using work computers. This uncertainty may cause them to seek employment elsewhere.
- Identity Theft: Some forms of monitoring may capture enough personal information that it could affect an employee’s personal security. For example, attackers could use the leaked data to perform targeted phishing attacks or bypass knowledge-based multi-factor authentication.
Resource & Financial Requirements
Another con of employee monitoring is the cost of purchasing, deploying, and managing the solution.
Monitoring employee computer activity generates a large volume of data. Actively reviewing employee reports may be viable for a small business but it is not scalable, nor is it an efficient use of employee time for most use cases.
For this reason, the majority of organizations will not actively examine each employee. Instead, they will limit auditing to an as-needed basis or when the software alerts them to specific activities that they are monitoring.
Alerts are typically set for high-risk activities such as anomalous file transfers, attempts to visit inappropriate sites, or the use of unauthorized portable storage devices.
The costs of monitoring employees
- Employee Time: Reviewing reports costs valuable time. Businesses that deploy monitoring software need to plan how actively engaged they will be: Will reviews be limited to specific investigations and automated alerts or will a member of staff be responsible for regularly reviewing the data?
- Software: Any employee monitoring software that is suitable for businesses will come at a cost. The costs for these tools are typically charged on a per-user basis with the cost per user decreasing based on the volume of licenses purchased.
- Retention: If employees strongly object to being monitored there is a risk that the use of employee monitoring could decrease retention rates.
Employee Monitoring Software Case Studies
Shady Maple Transforms Their Productivity With Employee Computer Activity Insights
Shady Maple found CurrentWare during a significant period of growth in their company. As their number of employees grew, Shady Maple knew that they needed an employee productivity solution that could scale along with them.
Their old ways of managing employee internet abuse—manually checking each employee’s computer individually and hoping that they didn’t clear out their web history—would no longer be sustainable.
Since implementing CurrentWare’s employee internet management tools, Shady Maple’s operational efficiency has skyrocketed.
With CurrentWare in place, Shady Maple could review the web browsing, bandwidth consumption, and application usage of their entire workforce from a central console.
These insights helped Shady Maple answer key questions:
- Are employee performance issues being caused by excessive unproductive web browsing?
- What bandwidth hogs are slowing down the network, and who is responsible for the excessive bandwidth use?
- Are our employees spending the majority of their time on-task, or do particular distractions need to be limited?
Read Shady Maple’s story to learn more about how valuable insights into employee computer activity transformed their productivity.
User Activity Insights in Citrix Workspace Drives Software Adoption and Productivity for The Coding Network
Productivity-boosting software is a strategic investment that empowers businesses to optimize workflows, drive efficiency, and gain a competitive edge.
However, as new tools and processes are introduced some employees may be more reluctant than others to accept them.
In these cases businesses need insights into the employee experience to address any friction during the adoption of new tools.
For The Coding Network, one such tool was Citrix Workspace, a digital workspace solution that provides their 100% remote workforce with secure access to applications, virtual desktops, and data, regardless of their location or device.
Thanks to the insights provided by CurrentWare’s computer monitoring software, the Coding Network was able to identify software usage gaps and get their software adoption rate up to 100%.
Conclusion
Employee computer activity tracking tools are valuable assets for improving and maintaining productivity and security.
If you would like to use these tracking tools in your business you first need to understand the data privacy laws of your jurisdiction, determine how you will monitor employees’ activity in a way that is transparent and fair, and find the best employee monitoring software for your needs.
Improve Employee Productivity With
CurrentWare’s Remote Employee Monitoring Software
Ready to get advanced insights into how your employees spend their time? Reach out to the CurrentWare team for a demo of BrowseReporter, CurrentWare’s employee and computer monitoring software.
- Improve Productivity
Track unproductive web browsing and idle time to detect time-wasting - Save Time With Intuitive Reports
User-friendly reports make it easy to understand employee computer activity - Enhance Visibility
See how employees spend their time—even on Terminal Server and Remote Desktop Services!
Further reading
- Monitoring Employees: 6 Privacy Tips for Employers
- Privacy Rights Clearinghouse – Workplace Privacy and Employee Monitoring (US)
- General Data Protection Regulation (GDPR) – Official Legal Text (EU/EEA)
- Employee Privacy and Employee Monitoring: Best Practices for Balancing Productivity, Security, and Privacy (White paper)