CurrentWare’s Role in the HR Investigations Process
Workplace misconduct investigations are a critical role of the human resources department. When misconduct is reported the HR team needs reliable insights so they can take immediate action.
CurrentWare’s user activity monitoring, web filtering, and USB control software solutions provide the capabilities needed to prevent misconduct and investigate a complaint.
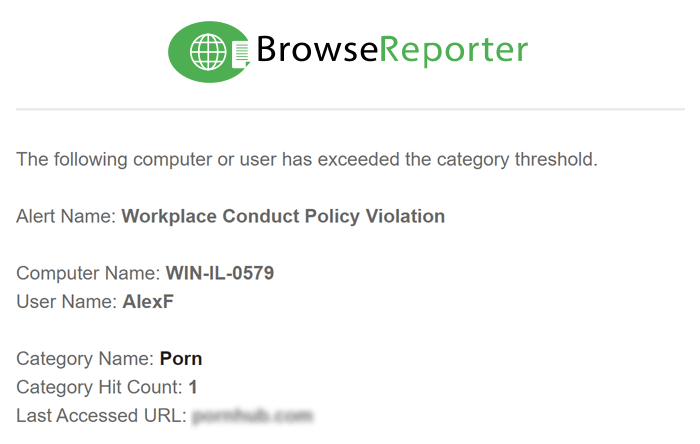
Get Alerts Of Company
Policy Violations
Proactively start workplace investigations before the complaint.
Send HR professionals alerts of inappropriate conduct on company devices to address policy violations before they escalate.
- Internet Abuse: Take appropriate action when employees visit high-risk, inappropriate, or unproductive websites. Maintain evidence of misuse to investigate any individuals involved.
- Support Disciplinary Action: Evidence of employee computer activity supports disciplinary action if an employee is found to have engaged in misconduct.
- Corrective Action: Discover opportunities to ensure that employees are properly trained in the acceptable use of workplace technology.
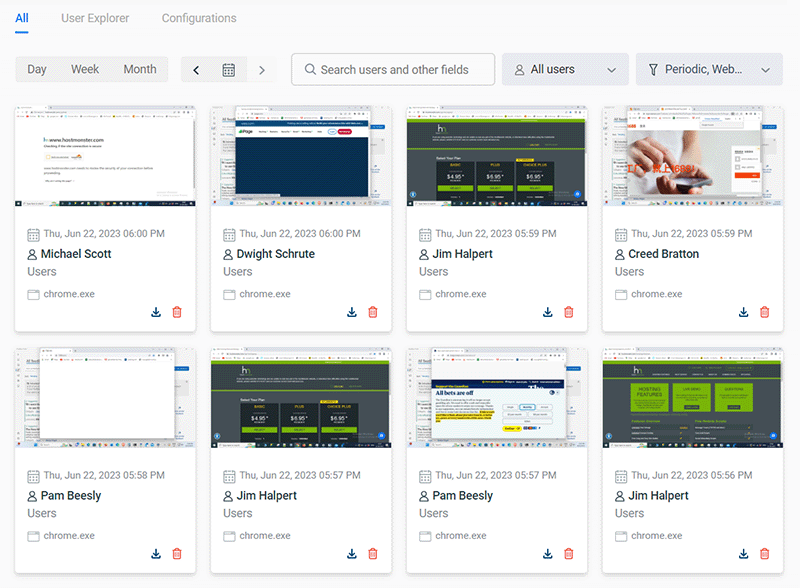
Automatic Screenshot Monitoring
Continuously capture screenshots for a visual record of employee activities. Compare productivity and activity data to the captured screenshots to understand exactly what your employees are doing.
- Capture screenshots at set intervals for specific users/computers
- Filter screenshots based on metadata such as productivity grading, application name, and user/PC
- Automatically delete screenshots based on age or storage use
Investigate Employee Complaints
CurrentWare’s PC activity logs give HR professionals the insights they need to investigate any employee accused of poor conduct.
- Investigate Harassment: Verify or refute allegations of misconduct on company computers with insights into web browsing, application use, and USB device usage.
- Support Internal Investigations: Empower Human Resources staff with the relevant data they need to conduct an investigation.
- Establish Patterns: Employee computer activity logs help establish a pattern of behavior that may indicate misconduct, such as excessive personal use of company resources and accessing inappropriate websites.
Detect & Prevent Employee Theft
Trusted insiders with access to sensitive information are a significant security threat.
CurrentWare helps prevent and detect insider threats with advance awareness and control over employee computer usage.
- Protect Data: Block access to cloud storage sites and limit removable media to authorized devices only.
- Detect Insider Threats: Receive real-time alerts when employees violate your acceptable use policies.
- USB Activity Monitoring: Track what data has been copied, created, deleted, or renamed on removable media to identify the source of a data breach.
Monitor as Discretely or Transparently as You Want
Whether you need discrete monitoring to capture evidence of misconduct or you want transparency to disincentivize inappropriate behavior, CurrentWare provides the capabilities you need.
- Stealth Mode: By default, the CurrentWare agent cannot be seen by employees
- Notifications: Optionally notify employees that they are being monitored with periodic popups
- Client Integrity: CurrentWare cannot be uninstalled or stopped without administrator privileges
Third Party Risk Management
Third-party vendors, partners, consultants, and contractors often have privileged access to a company’s internal systems.
Use CurrentWare’s data loss prevention and user activity monitoring features to detect high-risk behaviors from third party vendors.
- Continuously capture screenshots to collect evidence of misuse
- Monitor productivity of freelancers to ensure invoiced hours are used appropriately
- Track and restrict data movements to portable storage devices and cloud storage services to protect sensitive data
A Verizon report found that 35% of data breaches from 2023-2024 involved internal actors such as employees 1
CurrentWare’s employee investigation tools provide granular insights into high-risk user activities including file transfers to USB
52% of employees have experienced or witnessed inappropriate, unethical or illegal behaviors at work 2
Employee PC activity logs empower your HR team with the evidence they need to address these behaviors before they escalate
30% of employees who experienced inappropriate behaviors left the organization following the incident 2
With auditable records of user activity you can demonstrate your commitment to a safe and respectful work environment
See What Our Customers Have to Say
The reports are very easy to understand and the fact that they can be emailed to you on a schedule is amazing, and have made finding productivity killers VERY easy. Customer support has been fantastic every time I've had to reach out to them; I highly recommend them!
Kristen S, Associate IT Director
The Coding Network, 700+ Employees
As a 'novice' I was able to set up with help from support in about an hour. Previous software took forever and didn't work as advertised. This software worked right out of the box.
Dr. Gerard B, Office Manager
Medical Practice, 2-10 Employees
In my nearly 40 years in the IT business I’ve worked with a lot of support teams. I really appreciate CurrentWare going the extra mile to help me get the most out of the product. They’ve definitely outweighed any of the other competitors that I’ve looked at.
J.S, Managed Services Provider
Vehicle Dealership, 150-200 Employees
We have experienced data leaks by dishonest employees in the past and [CurrentWare's] AccessPatrol has helped us avoid them and work with greater security and peace of mind for us and our customers.
Julio V, Head of Information Technology
Financial Services Industry, 10,001+ employees
CurrentWare's Key Features
User Activity Monitoring
Track web browsing, software use, search queries, and more
Screenshot Monitoring
Take automatic screenshots or remotely view desktops
Track Software Usage
Get insights into software usage trends in your organization
Transparent & Stealth Modes
Run silently in the background or provide notice of monitoring
Block USB & Other Devices
Set full access, read only or no access on storage devices
Device Whitelist
Allow only authorized storage devices to be used
Block File Transfers
Prevent files from being transferred to portable storage
DLP Activity Reports
Track file transfers, storage device use, file operations, and more
Block Websites
Block websites based on
URLs & content categories
Block Downloads/Uploads
Prevent uploading and downloading based on file type
Application Blacklisting
Block specific Windows
applications from launching
PC Power Management
Remotely track and control PC power states
Central Web Console
Save time with a central admin console; optionally integrate Active
Directory OUs or security groups
Platform Security
Protect your CurrentWare console
with 2FA, passwords, privilege
management, and more
Offsite Management
Extend onsite security policies to computers running outside the corporate network
SQL Server Supported
Database scaled for enterprise and
large business operations using
Microsoft SQL Server
1 Verizon. (2024). (rep.). 2024 Data Breach Investigations Report. Retrieved from https://www.verizon.com/business/resources/reports/2024-dbir-data-breach-investigations-report.pdf.
2 HR Acuity. (2023). (rep.). 2023 Workplace Harassment and Misconduct Insights. Retrieved from https://www.hracuity.com/workplace-harassment-and-employee-misconduct-insights/.