Custom Security Policies
CurrentWare’s security policies can be uniquely customized for each group of users or computers.
- Block websites for some users and not others
- Restrict end-users while giving security teams greater flexibility
- Maintain custom security policies across all of your organization’s endpoints no matter which network they connect to
Restrict Access to High-Risk Sites
Enforce internet use policies, block distracting websites, and improve internet security with granular internet access control policies.
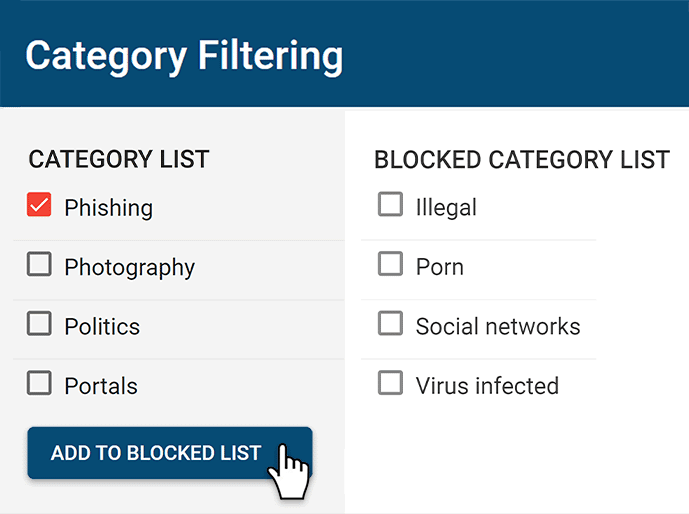
- Block websites based on URLs and content categories
- Effortlessly block millions of websites across 100+ URL categories
- Limit internet use to an Allow List for optimal endpoint security
Monitor User Devices for Events That Pose Security Risks
Your endpoint security depends on complete visibility into how your user accounts are interacting with your systems. CurrentWare helps provide visibility into risky behavior with intuitive user activity reports.
- Get alerts of high-risk user events and other security risks
- Monitor network traffic on endpoints for attempts to access high-risk websites and other policy violations
- Alert your network administrator, IT department, and other trusted users when high-risk events occur
Centralized Management for Scalable Data Protection
Implement data security policies from a central location. Easily monitor and control your entire workforce from the convenience of a web browser.
- Monitor & control each managed endpoint device from a central management console
- Place users/PCs in their own policy groups to apply a unique security policy to them
- Integrate with Active Directory to import & sync your organizational units or security groups to the CurrentWare Console
How to Improve Data Security With CurrentWare
The CurrentWare Suite provides critical security controls for protecting your network, endpoints, and sensitive data against a variety of high-risk activities.
Block & Audit Storage Devices
Control who can use portable storage devices and set security policies to limit what devices are allowed. Monitor data transfers to removable media and network storage devices to ensure that your data security policies are being followed.
Prevent Data Loss to Cloud Platforms
Protect sensitive data against the risks of cloud file sharing sites. Block cloud storage sites/apps, restrict uploads/downloads, and monitor file transfers for high-risk or anomalous activity.
Audit User Activity for Insider Threat Risks
Monitor employee computer usage for signs of insider threats. Track file transfers, web browsing, app use, and login/logout times for high-risk, anomalous, or inappropriate activity. Receive automated alerts straight to your inbox when specific events occur.
Block Data Transfers to Portable Storage & Uploads/Downloads
Go beyond simply blocking unauthorized devices; ensure optimal data protection with your trusted devices, too. Block file transfers to portable storage devices based on file extension and file name.
Use the File Filter to prevent the uploading and downloading of specific files such as EXEs.
Block High-Risk Network Ports
Block unused TCP/UDP ports to reduce the attack surface of your network. Improve data protection by mitigating the threat of data leakage over FTP, SFTP, IRC, and other high-risk network ports.
Block Risky Sites
BrowseControl’s web content category filtering database provides you with a convenient way to block millions of websites across over 100 URL categories. Easily block users from accessing social media, porn, games, known virus-infected websites, and more!
Why Use Endpoint Security Software?
Unmanaged endpoints pose a serious security vulnerability to your network.
Hackers will use your vulnerable endpoints as a front door to compromise the security of your network—Perimeter-based security simply isn’t enough to fight against these attacks.
As many businesses scale, their exposure to cybersecurity threats increases exponentially.
With CurrentWare’s endpoint security solutions you can protect data and business systems against common vulnerabilities including insider threats, unauthorized USB devices, and visits to high-risk websites.
35% of data breaches from 2023-2024 involved internal actors such as employees 1
Without an endpoint security software in place your next data breach may come from a trusted employee.
The global average cost of a data breach in 2023 was USD 4.45 million 2
Due to the cost of remediation, legal fines & threat responses even larger organizations can be devastated by an attack.
68% of respondents experienced recent endpoint attacks that compromised assets 3
Don’t let your employees be your weakest link; monitor employee computer activity to keep your business protected.
CurrentWare's Key Features
User Activity Monitoring
Track web browsing, software use, search queries, and more
Screenshot Monitoring
Take automatic screenshots or remotely view desktops
Track Software Usage
Get insights into software usage trends in your organization
Transparent & Stealth Modes
Run silently in the background or provide notice of monitoring
Block USB & Other Devices
Set full access, read only or no access on storage devices
Device Whitelist
Allow only authorized storage devices to be used
Block File Transfers
Prevent files from being transferred to portable storage
DLP Activity Reports
Track file transfers, storage device use, file operations, and more
Block Websites
Block websites based on
URLs & content categories
Block Downloads/Uploads
Prevent uploading and downloading based on file type
Application Blacklisting
Block specific Windows
applications from launching
PC Power Management
Remotely track and control PC power states
Central Web Console
Save time with a central admin console; optionally integrate Active
Directory OUs or security groups
Platform Security
Protect your CurrentWare console
with 2FA, passwords, privilege
management, and more
Offsite Management
Extend onsite security policies to computers running outside the corporate network
SQL Server Supported
Database scaled for enterprise and
large business operations using
Microsoft SQL Server
1 Verizon. (2024). (rep.). 2024 Data Breach Investigations Report. Retrieved from https://www.verizon.com/business/resources/reports/2024-dbir-data-breach-investigations-report.pdf.
2 IBM. (2023). (rep.). Cost of a Data Breach Report 2023. Retrieved from https://www.ibm.com/account/reg/us-en/signup?formid=urx-52258.
3 (2020). (rep.). The Third Annual Study on the State of Endpoint Security Risk. Retrieved from https://engage.morphisec.com/2020-endpoint-security-risk-study.