Best Alternatives to Kaspersky Endpoint Security for Business
Looking for the best Kaspersky alternatives for web control, USB device control, and user activity monitoring?
CurrentWare has the user activity tracking, web filtering, and data loss prevention security solutions you need to keep your business running securely and productively—at a fraction of the cost!
We offer fair prices and honest value to keep our products accessible to companies of all sizes.

Trusted by
& many more
Trusted by
& many more
CurrentWare’s Kaspersky Alternatives
Not Satisfied With Your Vendor?
Switch to Us & Get a Discount
Make the switch to CurrentWare today to save up to 25% on your first year!
Compare CurrentWare vs Kaspersky Key Features

| ✅ | Reports & Alerts | ✅ |
| ✅ | Remote Screen Capture | ❌ |
| ✅ | Scheduled Monitoring | ❌ |
| ✅ | Productive vs. Unproductive Time | ❌ |
| ✅ | Track Local Software Usage | ✅ |
| ✅ | Search Query Reports | ❌ |
| ✅ | Track File Transfers To/From Network Share Drives | ❌ |
| ✅ | Track Downloads/Uploads | ❌ |
| ✅ | Idle Time Tracking | ❌ |
| ✅ | Remote vs In-Office Tracking | ✅ |
| ✅ | Bandwidth Usage Tracking | ❌ |
| ✅ | URL Category Tracking | ✅ |
| ✅ | Audit Logons | ✅ |
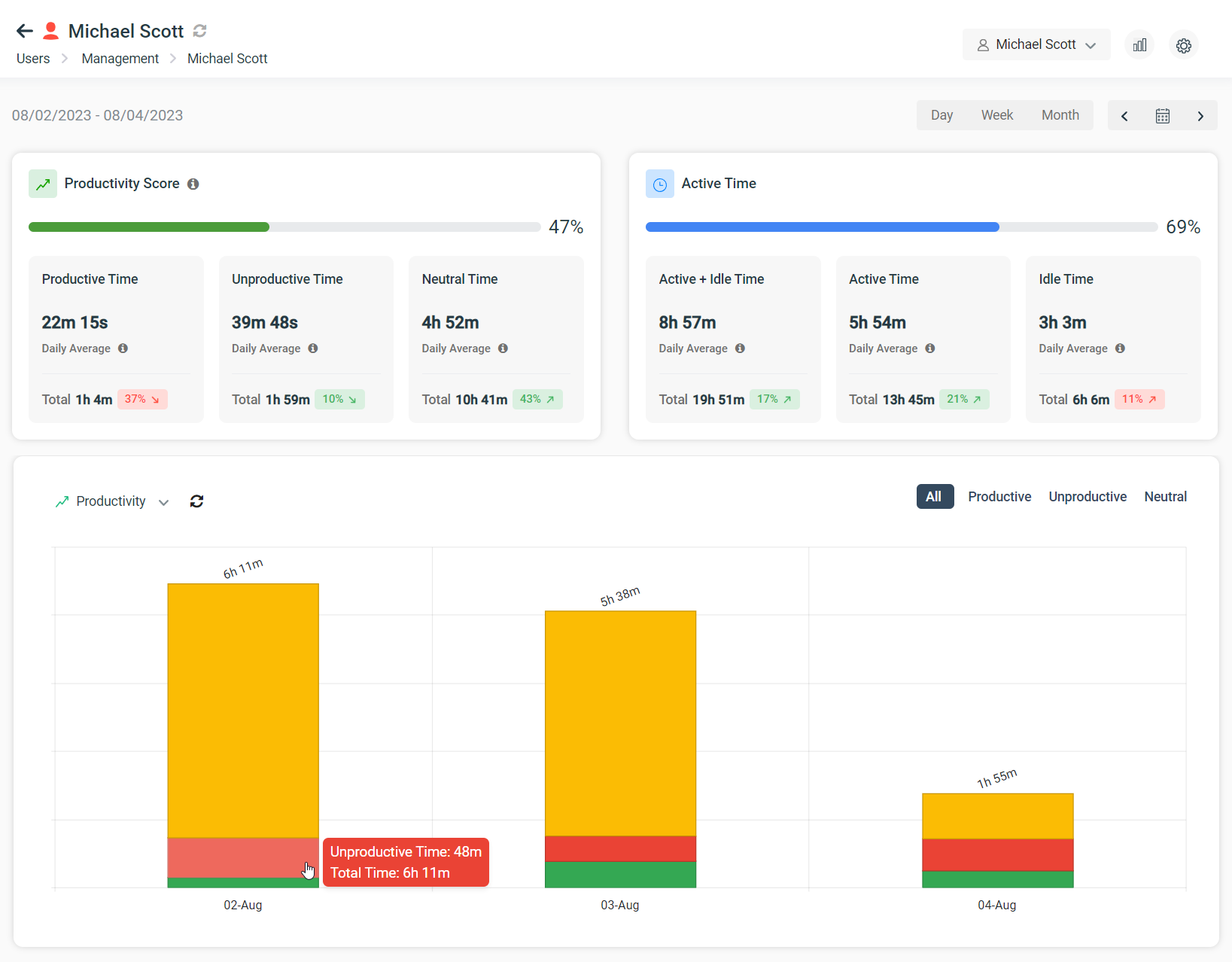
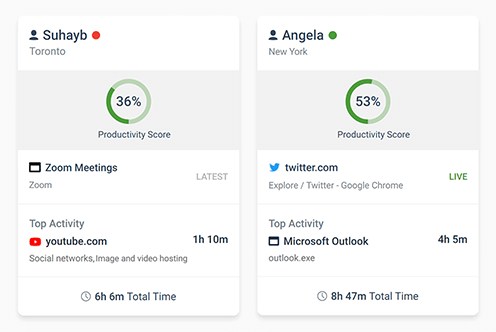
Employee Monitoring
This section will compare the employee monitoring software features of CurrentWare to Kaspersky Endpoint Security.
CurrentWare’s employee monitoring software gives you the internet and application usage data you need to track employee performance, monitor remote workers, and ensure that employees are following your acceptable use policy.
Last updated January 2023

| ✅ | Allow URLs & Domains | ✅ |
| ✅ | Block URLs & Domains | ✅ |
| ✅ | Scheduled Blocking | ❌ |
| ✅ | SSL Inspection | ✅ |
| ✅ | Time-Based Controls | ❌ |
| ✅ | Port Filtering | ✅ |
| ✅ | Block File Transfers to Cloud Storage | ❌ |
| ✅ | Block File Downloads/Uploads | ✅ |
| ✅ | Block Applications | ✅ |
| ✅ | Category Filtering | ✅ |
| ✅ | User Group Policies | ✅ |
| ✅ | Computer Group Policies | ✅ |
| ✅ | Custom Block Pages | ✅ |
| ✅ | Remote Workforce Management | ✅ |
| ❌ | Antimalware Scanning | ✅ |
| ✅ | Enforce Google SafeSearch | ✅ |
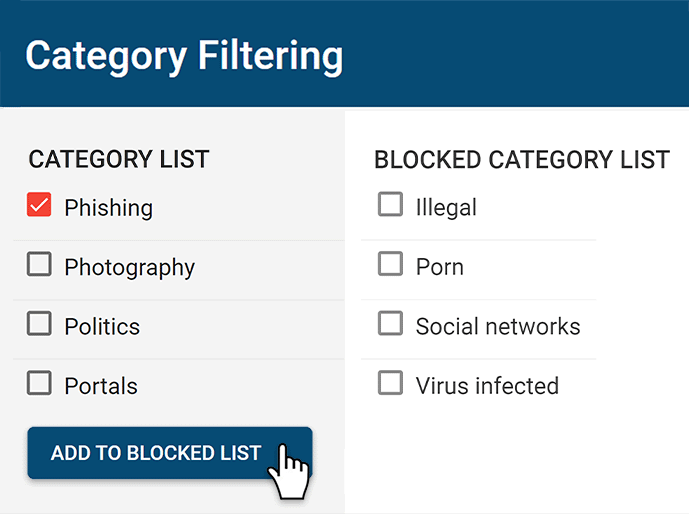
Web Filtering
This section will compare the web content filtering features of CurrentWare to Kaspersky Endpoint Security.
CurrentWare’s internet and application blocking software BrowseControl is a fantastic Kaspersky alternative for controlling employee internet use. It allows you to proactively block undesirable websites and applications to help keep your workforce secure and productive.
NOTE: Kaspersky Web Control is only available in the Kaspersky Endpoint Security Cloud Plus plan. On Windows workstations this component is unavailable if it is installed on a computer that runs on Microsoft Windows for file servers.
Last updated January 2023

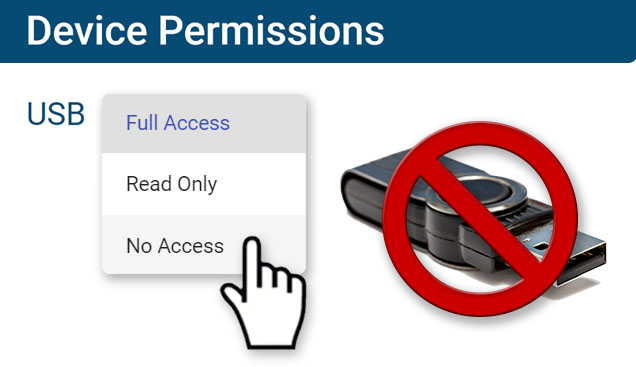
| ✅ | Block USB & Storage Devices | ✅ |
| ❌ | Malware Sandboxing & Antivirus Scanning | ✅ |
| ✅ | USB Activity Reports | ✅ |
| ✅ | Allow Trusted Peripherals | ✅ |
| ✅ | Block High-Risk Websites | ✅ |
| ❌ | Malicious Activity Rollback | ✅ |
| ❌ | Adaptive Anomaly Control | ✅ |
| ✅ | Block External Devices | ✅ |
| ✅ | Block USB File Transfers | ✅ |
| ✅ | SSL Inspection | ✅ |
| ✅ | Block File Transfers to Cloud Storage | ❌ |
| ✅ | Block File Downloads | ✅ |
| ✅ | Track File Transfers To/From Network Share Drives | ❌ |
| ✅ | Track Downloads/Uploads | ❌ |
Data Loss Prevention & Cybersecurity
This section will compare the data loss prevention and cybersecurity features of CurrentWare to Kaspersky Endpoint Security.
Monitoring and restricting USB file transfers is critical for protecting sensitive data against insider theft. CurrentWare’s AccessPatrol lets you restrict the use of a wide variety of peripheral devices including external storage hardware, Bluetooth, WiFi, and printers.
Note: Kaspersky’s USB device control features are only available in Kaspersky Endpoint Security Cloud Plus
Last updated January 2023

| ✅ | Central Admin Console | ✅ |
| ✅ | On-Premises | ✅ |
| ✅ Self-Managed Cloud |
Cloud Platform | ✅ |
| ✅ | Local & Remote Client Install | ✅ |
| ✅ | Command-line Deployment | ✅ |
| ✅ | Active Directory Installation | ✅ |
| ✅ | Active Directory Sync | ✅ |
| ✅ | Compatible with Windows | ✅ |
| ❌ | Compatible with MacOS | ✅ |
| ❌ | Compatible with Linux | ✅ |
| ❌ | Compatible with iOS/Android | ✅ |
| ✅ | Remote Workforce Management | ✅ |
Setup & Deployment
Getting started with CurrentWare is easy. CurrentWare offers a variety deployment options that suit the installation needs of organizations of all sizes.
Last updated January 2023

| 8:00 AM – 6:00 PM EST, Monday to Friday | Support Availability |
⚠️ Varies* |
| ✅ | Live Chat Feature |
⚠️ AI Chat Bot |
| ✅ | Phone Support | ✅ |
| ✅ | Training Videos | ✅ |
| ✅ | Email Support | ✅ |
| ✅ | Knowledge Base | ✅ |
Customer Support
Even the best vendors need to have a reliable support team to ensure that their customers get the services they need to make the most of their security solutions. This section will compare the customer support options of Kaspersky to CurrentWare’s Kaspersky alternatives.
*Kaspersky’s technical support availability varies based on whether or not you purchase a Maintenance Service Agreement (MSA). There are 4 MSA support tiers, with higher tiers offering faster response times.
Kaspersky’s Support Tiers:
- Standard Support: 10 am to 5 pm (ET) Monday – Friday
- MSA Start: 9 am to 7 pm (ET) Monday – Friday
- MSA Plus/Business/Enterprise: 24 x 7 x 365
Last updated January 2023
See What Our Customers Have to Say
The reports are very easy to understand and the fact that they can be emailed to you on a schedule is amazing, and have made finding productivity killers VERY easy. Customer support has been fantastic every time I've had to reach out to them; I highly recommend them!
Kristen S, Associate IT Director
The Coding Network, 700+ Employees
As a 'novice' I was able to set up with help from support in about an hour. Previous software took forever and didn't work as advertised. This software worked right out of the box.
Dr. Gerard B, Office Manager
Medical Practice, 2-10 Employees
In my nearly 40 years in the IT business I’ve worked with a lot of support teams. I really appreciate CurrentWare going the extra mile to help me get the most out of the product. They’ve definitely outweighed any of the other competitors that I’ve looked at.
J.S, Managed Services Provider
Vehicle Dealership, 150-200 Employees
We have experienced data leaks by dishonest employees in the past and [CurrentWare's] AccessPatrol has helped us avoid them and work with greater security and peace of mind for us and our customers.
Julio V, Head of Information Technology
Financial Services Industry, 10,001+ employees
Expand your capabilities with CurrentWare’s award-winning productivity and security software






Compare CurrentWare vs Kaspersky Endpoint Security Pricing
CurrentWare Pricing
CurrentWare’s Kaspersky alternatives are a cost effective solution for tracking the computer usage of your team members. CurrentWare offers fair prices and honest value to keep their products accessible to companies of all sizes.
CurrentWare’s solutions can be purchased individually for the greatest flexibility or as a full suite for the best value.
When purchased individually, the cost of BrowseReporter, BrowseControl, and AccessPatrol starts at $5 USD per user per month (paid annually). The full CurrentWare Suite includes all 4 modules starting at $12 USD.
Discounts Available:
- Pricing breaks are available for businesses that sign up for multi-year plans or have future growth planned and can commit to bulk orders.
- Volume license discounts are available starting for as low as 100 users, with discounts increasing depending on the number of licenses, and the length of the contract term.
- Educational organizations and nonprofits may qualify for a 10% license discount.
- Not satisfied with a competing vendor? Make the switch to CurrentWare today and you may save up to 25% on your first year!
Kaspersky Endpoint Security Pricing (10 Users)
- Endpoint Security Cloud: $535 USD/year
- Endpoint Security Cloud Plus: $820 USD/year
- Endpoint Security for Business Select: $595 USD/year
- Endpoint Security for Business Advanced: $1020 USD/year
*Pricing based on 10 users for 1 year; current as of November 2022.
CASE STUDY
Boston Centerless Scales Production & Secures Their Remote Workforce
CurrentWare has been nothing but supportive of us since we started. This is probably one of the best systems that we’ve ever invested in.
Once we got CurrentWare installed it opened the door for remote work for us; we could control the equipment and make sure our people were being productive and safe.
Why Choose CurrentWare’s Alternatives to Kaspersky?
Purchase the Exact Solutions You Need
Why pay for more features than you need? Each CurrentWare solution can be purchased individually, giving you access to the key features you need without paying for the features you don’t.

Use BrowseControl for Web Protection From Online Threats
BrowseControl’s internet security features include a web category filtering database to effortlessly block millions of websites across 100+ content categories. Easily block users from accessing social media, online storage, porn, games, known virus-infected websites, and more!
Block malicious websites on all your devices and as as many users as you need from the convenience of a central web console.
Enforce Acceptable Computer Use Policies
- Policy Reminders: Redirect users from restricted websites to your internet use policy or a custom block page
- Block Websites: Prevent access to websites that go against your acceptable computer use policies
- Non-Compliance Alerts: Combine BrowseControl with BrowseReporter internet use monitoring software to get alerts of policy violations
Block Bandwidth Hogs to Improve Network Availability
- Block Bandwidth Hogs: Block Netflix, Amazon Prime Video, and other unproductive bandwidth hogs
- Restrict Unproductive Sites: Reduce unproductive web browsing to ensure bandwidth availability for work tasks
- Discretionary Access: Selectively allow access to high-bandwidth sites on an as-needed basis
Reduce Distractions to Improve Employee Productivity
- Improve Focus: Block distracting websites and apps to keep your users focused on their tasks
- Custom Internet Policies: Apply different policies for group of users or computers to avoid bottlenecks
- Control Tech Use: Combine with BrowseReporter computer monitoring software for advanced awareness and control over technology usage
Protect Your Business From Compliance & Liability Risks
- Prevent Software Piracy: Use the app blocker to prevent employees from launching specific applications
- Block Inappropriate Content: Prevent users from accessing pornographic, hateful, or crude websites at work or school
- Meet Compliance Requirements: Control internet use to secure your network against web-based threats and data loss to cloud storage sites/apps
Protect Against Web Security Threats
- Download Blocker: Block file downloads such as executables, zipped files, and videos from the internet
- Internet Off: Block the entire internet from being browsed for specific computers or employees
- Malware Protection: Block malicious and high-risk websites with our frequently updated category filtering database
Prevent Data Theft & Leakage
- Cloud DLP: Block unsanctioned cloud storage apps and sites to prevent employee data theft
- Port Filtering: Block ports used for FTP, SCP, SFTP, etc. to prevent data from leaving the network
- Block High-Risk Sites: Block other potential data egress points such as personal email platforms, torrenting sites, etc
Try Our Kaspersky Alternatives for Free
Fully functional. Easy to use. Install in minutes.
CurrentWare's Key Features
User Activity Monitoring
Track web browsing, software use, search queries, and more
Screenshot Monitoring
Take automatic screenshots or remotely view desktops
Track Software Usage
Get insights into software usage trends in your organization
Transparent & Stealth Modes
Run silently in the background or provide notice of monitoring
Block USB & Other Devices
Set full access, read only or no access on storage devices
Device Whitelist
Allow only authorized storage devices to be used
Block File Transfers
Prevent files from being transferred to portable storage
DLP Activity Reports
Track file transfers, storage device use, file operations, and more
Block Websites
Block websites based on
URLs & content categories
Block Downloads/Uploads
Prevent uploading and downloading based on file type
Application Blacklisting
Block specific Windows
applications from launching
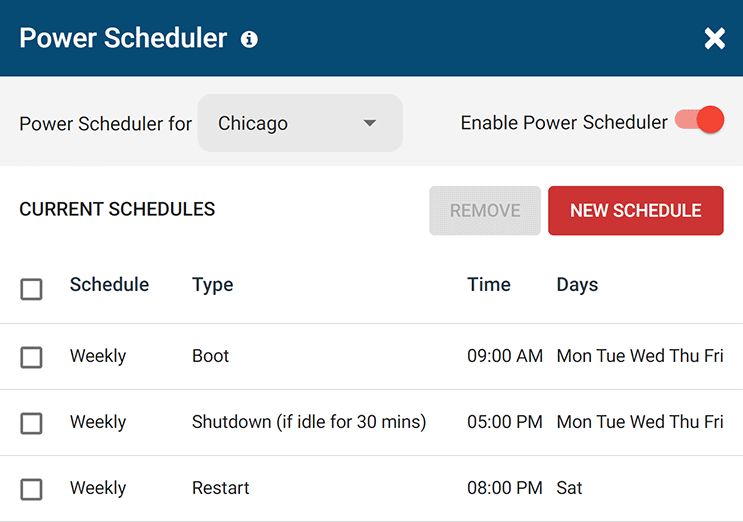
PC Power Management
Remotely track and control PC power states
Central Web Console
Save time with a central admin console; optionally integrate Active
Directory OUs or security groups
Platform Security
Protect your CurrentWare console
with 2FA, passwords, privilege
management, and more
Offsite Management
Extend onsite security policies to computers running outside the corporate network
SQL Server Supported
Database scaled for enterprise and
large business operations using
Microsoft SQL Server
Get Advanced Activity Insights
BrowseReporter is a versatile computer activity monitoring software to track productivity, web browsing, and app use
- Make informed decisions
- Enforce company policies
- Improve productivity
Block Harmful Websites
BrowseControl is an easy-to-use website blocking software for restricting internet access
- Block URLs & categories
- Block unwanted apps
- Website allow & block lists
Stop Data Theft to USB Devices
AccessPatrol is USB control software to protect sensitive data against theft to portable storage devices
- Block USB devices
- USB file activity alerts
- Block file transfers
Control PC Power States
enPowerManager is a remote PC power manager for centrally managing power settings across all endpoints.
- Track logon and logoff times
- Log PC power event history
- Remotely shutdown PCs
What Happened to Kaspersky?
“The company Kaspersky Lab has faced controversy over allegations that it has engaged with the Russian Federal Security Service (FSB) to use its software to scan computers worldwide for material of interest—ties which the company has actively denied.
The U.S. Department of Homeland Security banned Kaspersky products from all government departments on 13 September 2017, alleging that Kaspersky had worked on secret projects with Russia’s Federal Security Service (FSB).
In October 2017, subsequent reports alleged that hackers working for the Russian government stole confidential data from the home computer of a National Security Agency contractor in 2015 via Kaspersky antivirus software.
Kaspersky denied the allegations, stating that the software had detected Equation Group malware samples which it uploaded to its servers for analysis in its normal course of operation.” – Wikipedia
What is Kaspersky Endpoint Security?
Kaspersky Endpoint Security is an endpoint security software to protect endpoint devices such as workstations used in businesses.
The software includes features for application control, device control, web control, web activity monitoring, device use monitoring, and application monitoring.
The CurrentWare Suite is the best Kaspersky competitor for blocking websites, preventing a data breach to USB devices, and monitoring the internet usage of your users.
Try Our Kaspersky Alternatives for Free
Fully functional. Easy to use. Install in minutes.