Protect Sensitive Data With Our Robust File Activity Monitoring Software
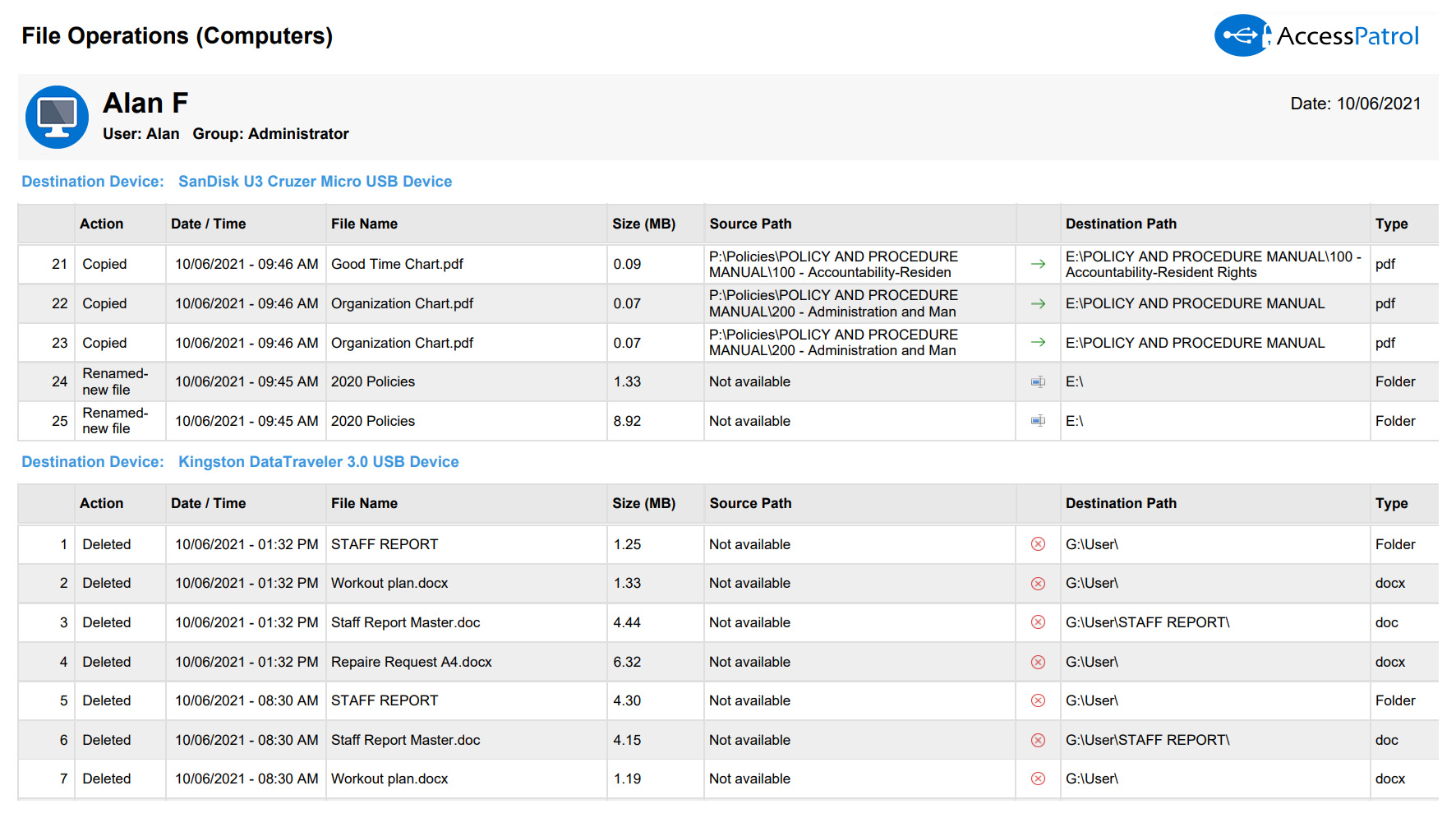
File Transfer Monitoring
- Track files that are copied to portable storage devices, network share drives, cloud storage services, and more
- Selectively choose which file operations to include in the report, such as tracking files copied to cloud storage services
- Track file transfer history based on individual users and computers as evidence of who copied data
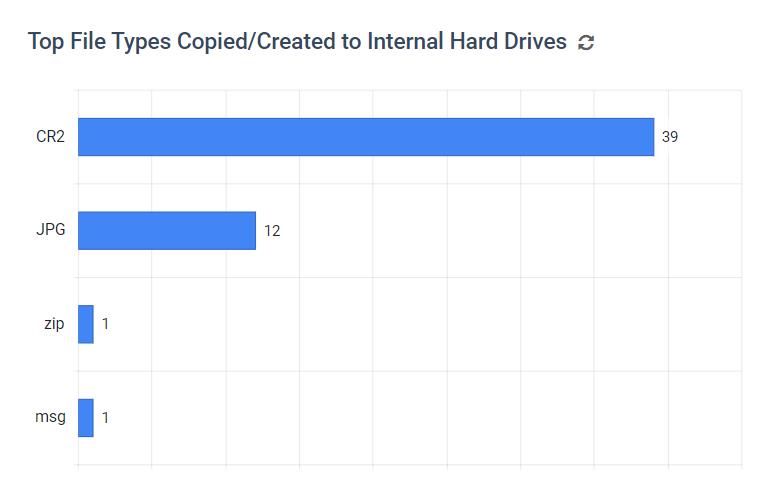
Top File Types Copied/Created
- See what file types are commonly transferred to internal hard drives and external devices
- Find out which groups and users/PCs use removable media device the most
- Review the Activity Log for specific details on what files are being transferred and by who
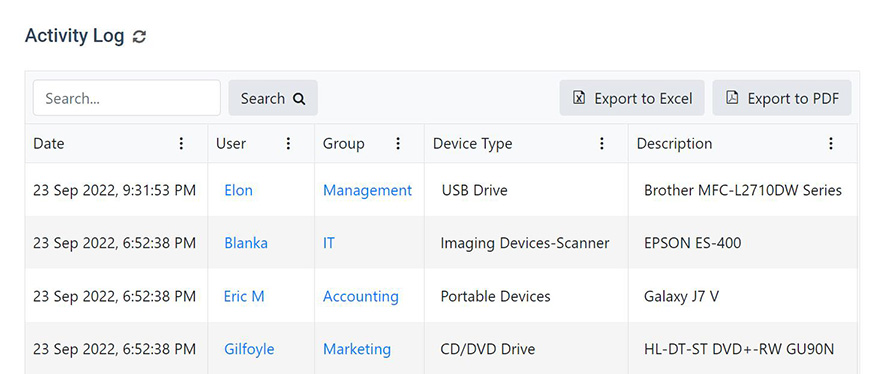
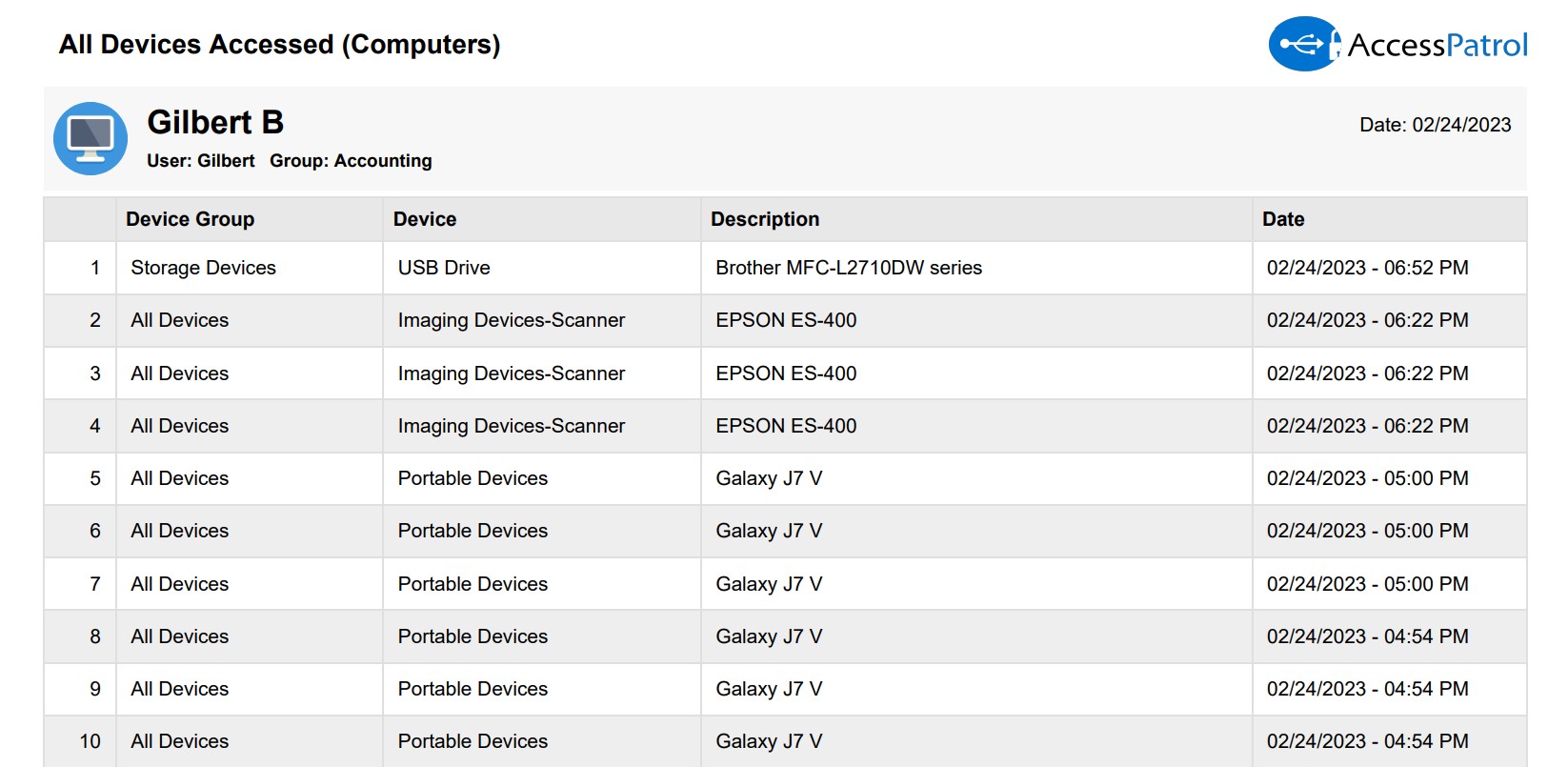
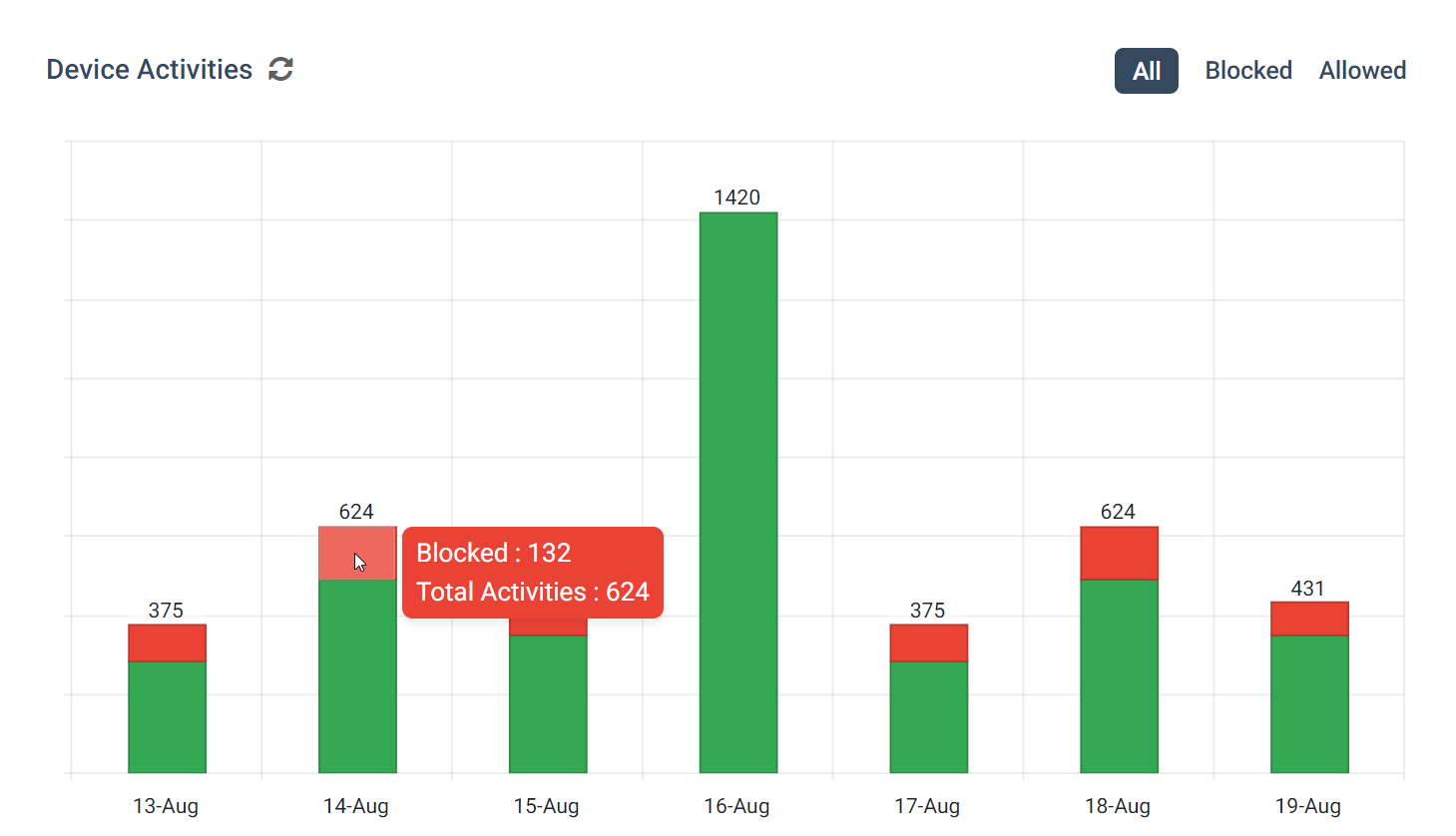
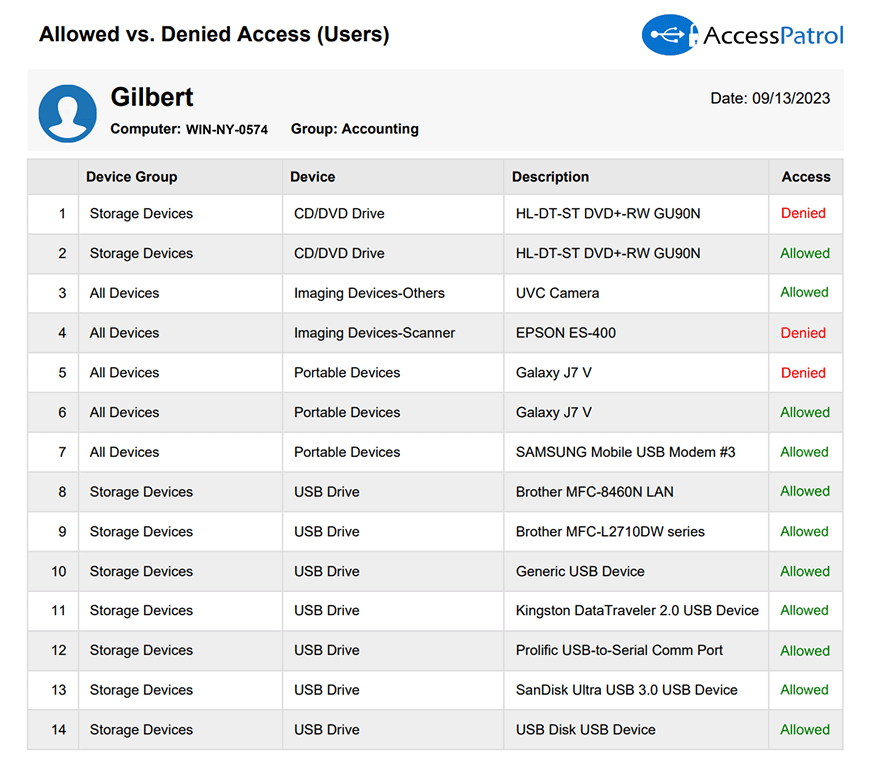
USB History Reports and Dashboards
- Track USB drive usage, previously connected storage devices, wireless devices, imaging devices, and other peripherals
- Drill down into the USB drive usage history of specific users or computers
- Retain USB drive usage history data with date and time, user/computer name, policy group name, device type, description, and allowed vs blocked status
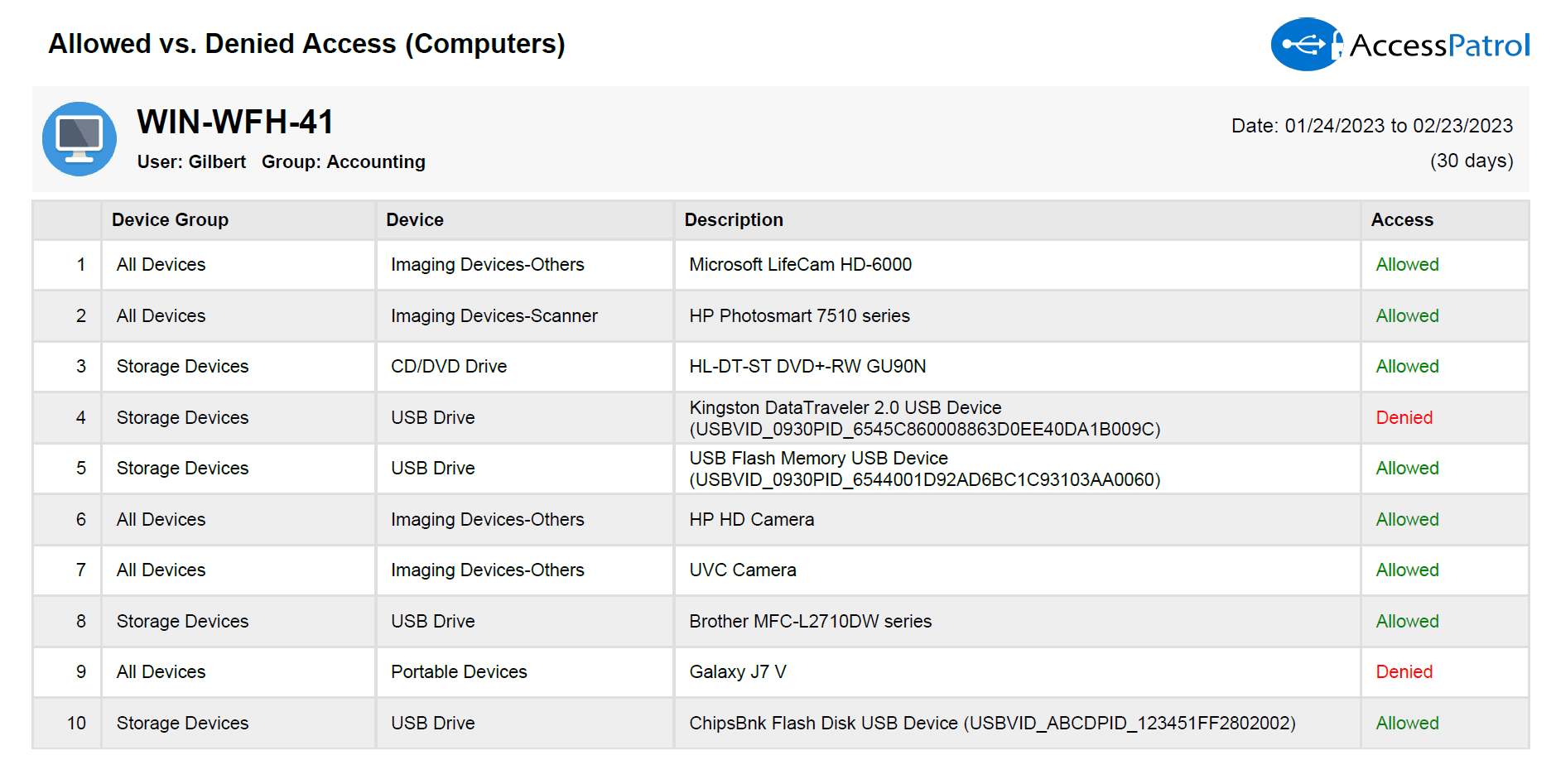
Track Usage of Allowed vs Denied USB Drives
- Collect evidence of users attempting to use unauthorized portable storage devices
- Alert IT security teams to high-risk USB activities such as transferring sensitive data to a USB stick
- Find out which groups require further USB security training
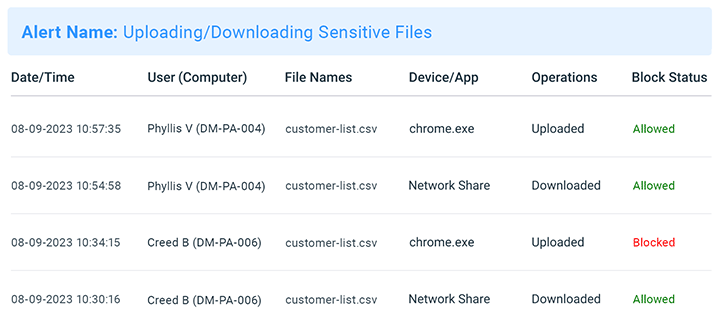
Track & Block File Transfers to Cloud Storage Services
- Detect when an employee uploads company IP to the cloud
- Track what files are uploaded and downloaded on any website
- Block file uploads to cloud storage service websites and apps
Protect Sensitive Files With File Activity Monitoring Alerts
AccessPatrol’s real time monitoring provides your organization with the file activity monitoring tools it needs to protect important files against insider threats.
Instantly notify designated people of high-risk data movements to quickly identify attempts to transfer sensitive information to external drives, removable devices, cloud storage services such as Google Drive, and network share drives.
-
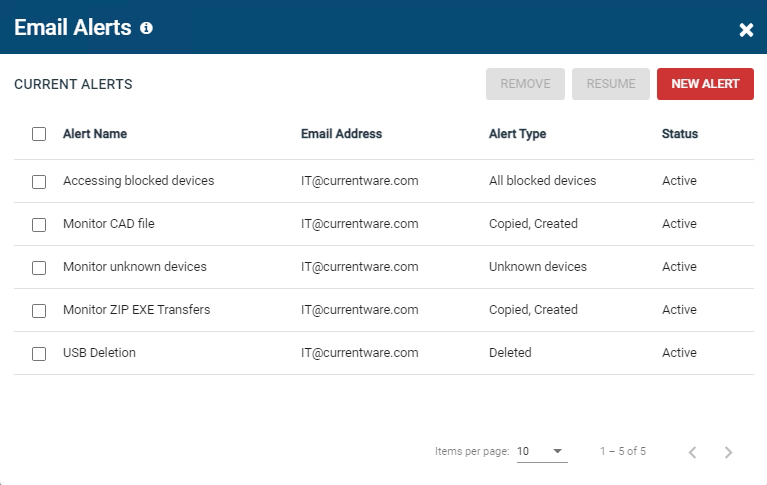
File Activity Alerts: Send AccessPatrol’s reports straight to your security team’s inbox when alerts are triggered
-
USB Data Loss Prevention: Customize thresholds to send email alerts based on suspicious USB connection history, file operations, or specific file types
-
Removable Media Control: Combine the USB security alerts with AccessPatrol’s other USB control features to enforce your removable media device policy and improve your USB data loss prevention capabilities
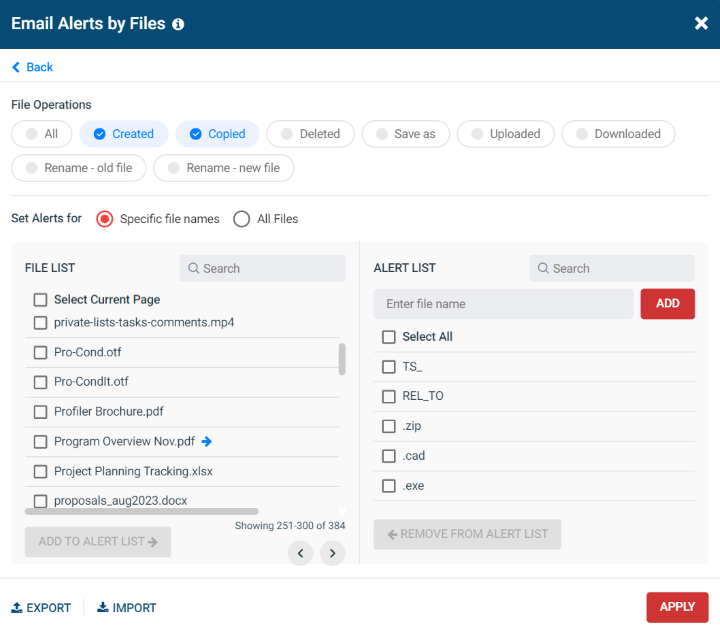
USB File Operations Alerts
Protect sensitive data against theft by alerting security personnel when suspicious file operations are performed on USB storage devices, cell phones, and cameras.
Configure file operations alerts based on file extensions (.exe, .zip, .msi, .xslx, .cad, etc) or file names to get alerted when these copied files are detected.
You can configure file operations alerts to trigger when:
- Files are created on external storage devices
-
Files are transferred to external storage devices
-
Files are deleted from external storage devices
-
Files are saved as to external storage devices
-
Files are renamed on external storage devices
Get Alerted When Sensitive Files Are Transferred
Get advanced alerts of suspicious activity, such as when specific file types and file names that are likely to contain sensitive data are transferred to removable devices.
You can configure file activity alerts to trigger when:
-
A user commits any sort of file operation
- A user transfers specific file types
-
A user transfers files with pre-defined keywords in the file name
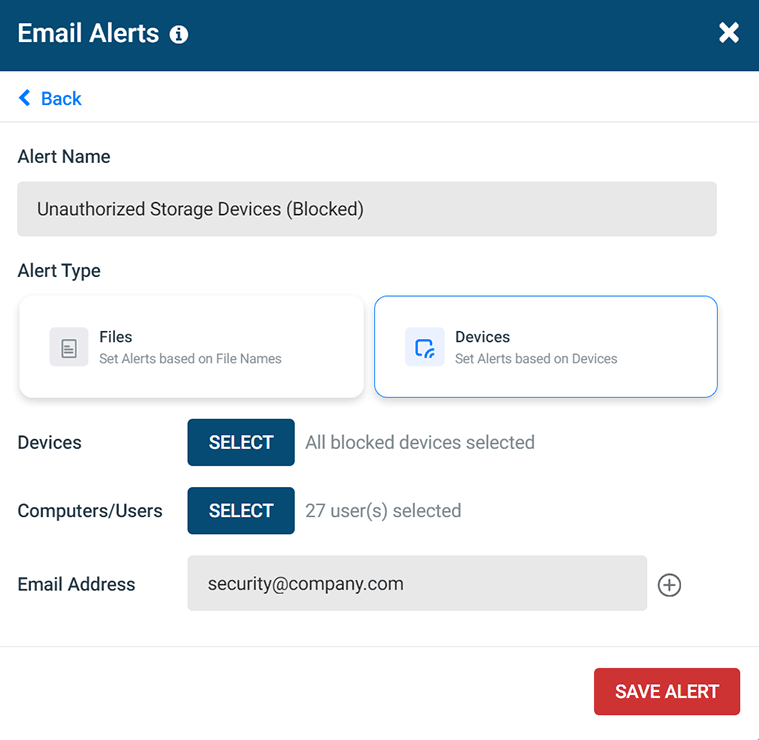
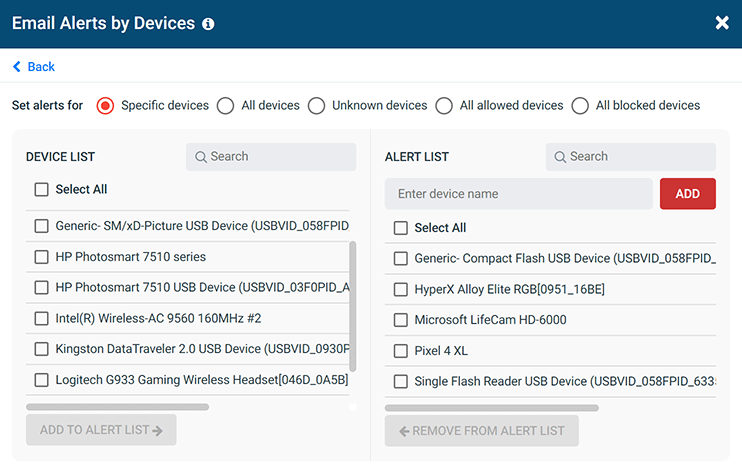
USB Device Usage Alerts
With the Email Alerts by Devices feature you can trigger real-time usb security alerts based on the peripheral device usage of your organization
You can configure USB connection history alerts to trigger when:
- A Specific USB device is used
- Any USB device is used
- An unknown USB device is used
- Users are denied access to removable media
FREE DOWNLOAD
Removable Media Policy Template
Download this data security policy template to prevent data leakage to USB flash drives and other removable storage devices.
- Set data security standards for portable storage
- Define the acceptable use of removable media
- Inform your users about their security responsibilities
AccessPatrol’s USB Control & Data Loss Prevention Features
Block USB & Other Devices
Set full access, read only or no access on storage devices
Whitelist USB Devices
Allow only authorized storage devices to be used
Block File Transfers
Prevent files from being transferred to portable storage
Access Code Generator
Provide temporary access to peripheral devices
DLP Activity Reports
Track file transfers, storage device use, file operations, and more
File Transfer Monitoring
Monitor files that are copied to USBs, cloud storage, and more
Alerts & Reports
Automatically send USB activity reports to designated inboxes
Transparent & Stealth Modes
Run silently in the background or provide notice of monitoring
Central Web Console
Save time with a central admin console; optionally integrate Active
Directory OUs or security groups
Platform Security
Protect your CurrentWare console
with 2FA, passwords, privilege
management, and more
Offsite Management
Extend onsite security policies to computers running outside the corporate network
SQL Server Supported
Database scaled for enterprise and
large business operations using
Microsoft SQL Server