4.8/5 on G2 Trusted by 100,000+ professionals in 55 countries
Drive Performance & Oversight for Your Remote Workforce
Monitor activity, reduce insider risks, and improve productivity – all from one platform. The CurrentWare Suite gives you the visibility and control needed to manage remote and hybrid teams without compromising trust.
Track activity & attendance
Prevent data loss
Optimize workforce performance
No credit card required.
Location Based
Track productivity anywhere
Smart Attendance
Verify without micromanaging
$6/User
Affordable remote management
Trusted by local and state government agencies , healthcare organizations, professional services firms, and more.
Improve Productivity
81%
Detect Time Theft
52%
of employers have found an employee working a second job while on the clock, thanks to monitoring software
Optimize Software Spend
36%
of desktop software & 29% of SaaS spend is underutilized or wasted, according to Flexera’s State of ITAM 2023 report
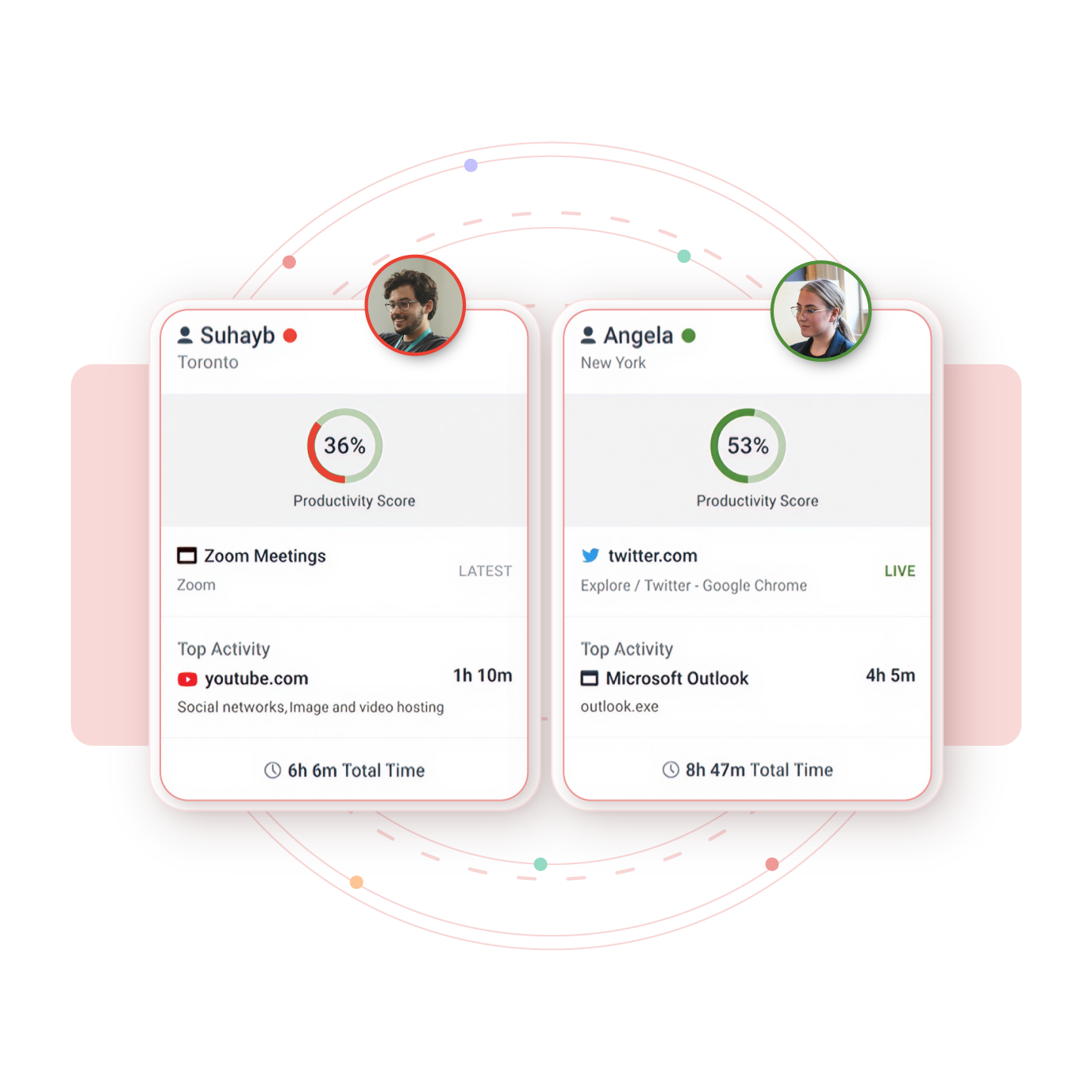
Gain Full Visibility Into Your Remote Workforce
- Remote work removed the walls, CurrentWare brings back the context-without crossing privacy boundaries
- BrowseReporter turns activity into patterns, not suspicion
- Understand who’s thriving, who’s overloaded, and where time quietly slips away
- Employees access their own productivity dashboards
- Visibility that builds trust not tension.

Key benefits
Work From Home Policy Template
FREE DOWNLOAD
Download this free work from home policy template and tailor it to fit your company’s needs
- Set expectations for employees who work from home
- Define eligibility criteria for working remotely
- Outline your remote employee monitoring practices
Keep Your Data Safe and Prevent Insider Risks
When teams work remotely, your perimeter stretches thin. Shadow IT, accidental leaks, and insider risks can quietly erode your security posture. CurrentWare’s remote workforce management safeguards the edge – quiet, protective, always on.
Restrict USB and peripheral access
Block unsafe or non-compliant websites
Monitor file movement across endpoints
According to the Code42 Data Exposure Report 2024, 80% of cybersecurity leaders admit departing employees have taken valuable IP. With centralized monitoring, CurrentWare helps ensure your data stays where it belongs—securely inside your organization.
PROVEN RESULTS
Real Results & Validation
BrowseControl is trusted by businesses worldwide to improve productivity and compliance.


Track Attendance and Performance in Real Time
No more guessing who’s productive and who’s merely online. CurrentWare’s remote employee management software turns attendance into insight, so managers can coach with confidence, not suspicion.
You can
Fair visibility, powered by data—not doubt.
Improve Hybrid Workforce Productivity
Monitoring is the start; optimization is the payoff. With Workplace productivity insights, patterns inside the workday surface – too many meetings, too little focus time, licenses paid for but rarely used.
How CurrentWare Helps Teams Work Smarter, Safer, and With Greater Clarity
Every remote workplace tells a different story. For each, CurrentWare’s suite delivers one promise: clarity without compromise.
Turn Uncertainty Into Insight
(Powered by BrowseReporter)
For hands-on IT leaders, BrowseReporter turns speculation into insight. It shows which applications power real work and which drain hours into the ether.
CurrentWare saved us a lot of time and money. If we didn’t have them we would’ve never known what was going on. I can’t thank all of you enough for this software.”
– Vincent Pecoreno, Network Administrator, Viking Yachts
Create Focused Digital Workspaces
(Powered by BrowseControl)
Remote work multiplies distraction. BrowseControl lets teams create digital boundaries that protect focus and compliance without stifling autonomy.
- Block unsafe or non-compliant sites
- Schedule access by time or department
- Reduce downtime and cyber risk across distributed endpoints
CASE STUDy
Shady Maple Transforms Their Productivity With Internet Filtering
“Being able to identify negative browsing trends and put a stop to them within a couple of hours has meant that our employees are focused on the job almost all of the time. We have become an extremely efficient workforce.”
– Operations Management, Shady Maple

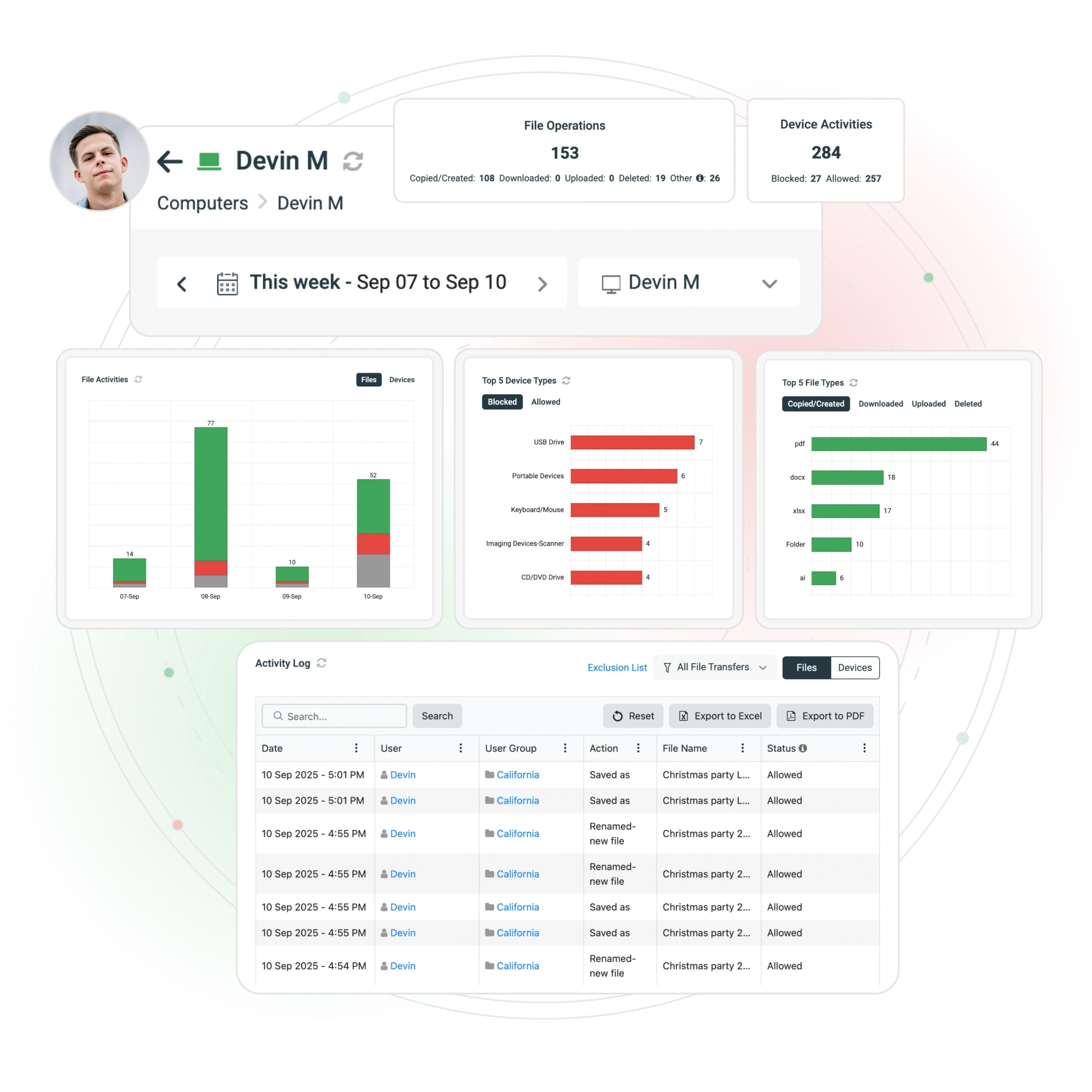
Protect Data at the Edge
(Powered by AccessPatrol)
Tiny devices, big risk. AccessPatrol prevents sensitive data from walking out the door—literally.
- Enforce USB and peripheral restrictions
- Track file transfers in real time
- Revoke access instantly for departing employees
“We never have to worry when someone plugs in a device. AccessPatrol made our lives easy. We just set it, forget it, and it works.”
– Nicholas Scheetz, IT Service Desk Supervisor, First Choice Health
Hospitals protect PHI. Financial firms safeguard client records. Manufacturers lock down CAD files and IP.
Reduce Waste Automatically
(Powered by enPowerManager)
When the CFO examines the ledger, enPowerManager turns IT from cost center to quiet hero.
- Automates workstation shutdowns
- Cuts power waste by up to 30%
- Supports ESG and cost-reduction goals
CASE STUDy
Shady Maple Transforms Their Productivity With Internet Filtering
“CurrentWare has been nothing but supportive of us since we started. This is probably one of the best systems that we’ve ever invested in. Once we got CurrentWare installed it opened the door for remote work for us; we could control the equipment and make sure our people were being productive and safe.”
-Boston Centerless
One regional healthcare client saved $12,000 in a quarter and trimmed its carbon footprint at the same time.

Ensure Compliance & Audit Readiness
In regulated sectors, compliance isn’t optional – it’s oxygen. CurrentWare’s remote workforce monitoring software keeps you audit-ready with verifiable trails and right-sized controls
Why Choose CurrentWare for Remote Workforce Management
Works on-premise or in the cloud
Centralized visibility for distributed teams
Granular privacy controls for ethical monitoring
20+ years in endpoint and workforce analytics
Trusted across law, healthcare, finance, and manufacturing
How to Choose Remote Employee Management Software
- Choose clarity, not surveillance: Look for privacy-first, ethical insights, not keyloggers or intrusive tracking.
- Prioritize security at the edges: Ensure USB control, file tracking, and web filtering protect the places remote work is vulnerable.
- Deploy quickly with low IT burden: The best tools install fast, integrate cleanly, and don’t need outside consultants.
- Demand measurable ROI: From license optimization to risk reduction, your software should pay for itself, fast.
Benefits for Every Stakeholder
- Deploys in hours, not months
- Gains endpoint control without enterprise bloat
- Reduces emergencies, shadow IT, and helpdesk chaos
- Walks into audits with confidence
- Cuts software waste and unnecessary spend
- Reduces breach risk and compliance penalties
- Sees ROI in real numbers, not promises
- Improves revenue-per-employee
- Uses objective data to support fairness
- Identifies burnout risks early
- Communicates transparently with privacy-first reporting
- Strengthens trust between managers and teams
- Gains visibility without becoming a micromanager
- Strengthens operational consistency
- Scales growth without scaling headcount
- Leads with clarity instead of guesswork
Frequently Asked Questions
Remote employee management software helps organizations monitor, support, and optimize the productivity of employees who work from home, hybrid, or distributed locations. It provides visibility into app usage, work patterns, and team workloads to improve efficiency and decision-making.
Organizations use remote employee management software to understand how remote teams work, identify productivity barriers, prevent burnout, and ensure accountability. It enables managers to make data-driven decisions about workflows, staffing, hybrid policies, and performance improvement.
CurrentWare collects data on application usage, website activity, productive time, idle time, and workload trends. A lightweight agent runs on employee devices and sends activity insights to centralized dashboards—without invasive tracking methods like keylogging, webcam access, or stealth recording.
Remote employee management software focuses on productivity insights, workflow improvement, and operational efficiency. Surveillance tools use intrusive methods such as keystroke logging or secret screen capture. CurrentWare is privacy-respectful, transparent, and designed to support—not spy on—remote teams.
Top metrics include:
- Productive vs unproductive time
- Active vs idle hours
- Application & website usage
- Workload balance and burnout risk
- Focus on time and task efficiency
- Productivity trends across remote vs. office staff
These insights help managers optimize performance and support teams more effectively.
Yes. Ethical platforms like CurrentWare offer customizable privacy controls, data minimization options, and no keystroke logging. Companies can define what is tracked, anonymize data where needed, and use clear communication to maintain employee trust in remote or hybrid work environments.
Yes, when used transparently and for legitimate business needs. Organizations should notify employees, follow local labor & privacy laws, and implement clear monitoring policies. CurrentWare supports compliance with GDPR, ISO standards and internal governance requirements.
Key organizational benefits include:
- Improved productivity visibility
- Better workload distribution
- Reduced burnout risk
- Insights into software usage & license optimization
- Increased accountability in remote teams
- Stronger hybrid work policy decisions
- Enhanced security & compliance posture
- Set goals for productivity, compliance, and workforce optimization
- Deploy the CurrentWare agent to remote and hybrid devices
- Communicate your monitoring policy to employees
- Review dashboards for productivity, app usage, and workload insights
- Use the data to coach teams, allocate resources, and refine workflows
CurrentWare is fast to deploy, easy to manage, and ideal for remote workforce management.
CurrentWare’s BrowseReporter tracks mouse/keyboard inactivity. With its “Idle Exclusion” feature, you can exclude certain apps (like meeting tools) from being classified as idle, leading to more accurate productivity data.
Yes — through device control (e.g., USB restrictions), file transfer tracking, and web filtering. These features help you secure data on remote endpoints and reduce insider risk.
Real‑time alerts help managers identify policy violations, schedule deviations, or suspicious inactivity (like “mouse jigglers”) as they happen, enabling quick intervention and more reliable workforce oversight.