Why Should I Block Cell Phones from Connecting to Computers?
The use of personal cell phones in the workplace is not just a distraction, they are also a high-risk device that needs to be addressed as part of your endpoint security policy.
Data security risks of cell phones
- Data Exfiltration: Unless you assign read-only access to mobile devices, employees can connect their phones to their workstations and illicitly transfer data to their smartphone’s microSD card or internal storage.
- Mobile Malware: Worms, trojans, and other malicious software can be unknowingly transferred to and from mobile devices. All it takes is an employee with Full Access permissions to plug their compromised device into their computer for the attack to begin.
How to Protect Data Against Mobile Devices With AccessPatrol
- Disable Bluetooth on workstations to prevent wireless data transfers to cell phones
- Block cell phones, iPods, PDAs, and other mobile devices from connecting to computers
- Monitor device reports and removable media file transfer logs for suspicious behavior
- Provide employees with alternatives for charging their phones such as USB ports in wall outlets and power bars
AccessPatrol’s USB Control & Data Loss Prevention Features
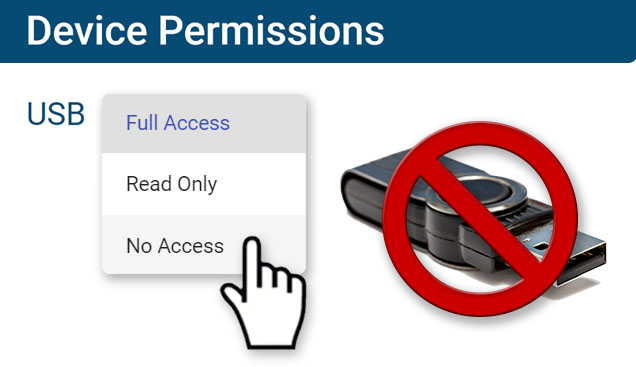
Block USB & Other Devices
Set full access, read only or no access on storage devices
Whitelist USB Devices
Allow only authorized storage devices to be used
Block File Transfers
Prevent files from being transferred to portable storage
Access Code Generator
Provide temporary access to peripheral devices
DLP Activity Reports
Track file transfers, storage device use, file operations, and more
File Transfer Monitoring
Monitor files that are copied to USBs, cloud storage, and more
Alerts & Reports
Automatically send USB activity reports to designated inboxes
Transparent & Stealth Modes
Run silently in the background or provide notice of monitoring
Central Web Console
Save time with a central admin console; optionally integrate Active
Directory OUs or security groups
Platform Security
Protect your CurrentWare console
with 2FA, passwords, privilege
management, and more
Offsite Management
Extend onsite security policies to computers running outside the corporate network
SQL Server Supported
Database scaled for enterprise and
large business operations using
Microsoft SQL Server