How to Monitor Application Usage on Windows Computers

How to Monitor Windows Application Use With BrowseReporter
NOTE: The above video features a legacy user interface for BrowseReporter. To see the latest features and interface please visit the BrowseReporter product page.
CASE STUDY
Activity Insights in Citrix Workspace Drives Software Adoption and Productivity
2022 Updates
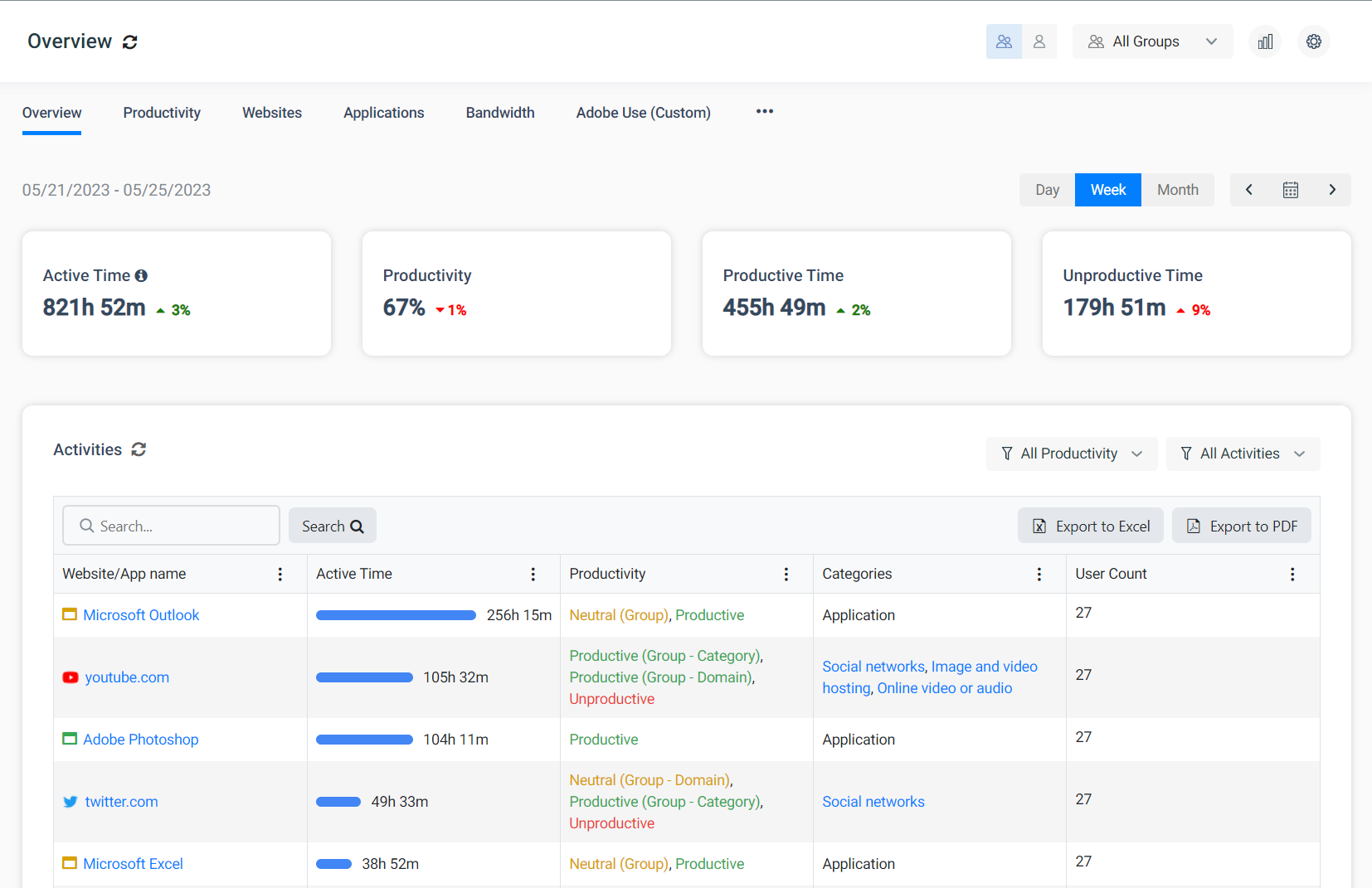
A lot has changed in BrowseReporter since this video was introduced; BrowseReporter’s new user activity dashboards provide further insights into what software your employees use.
Original Video Transcript
Thanks for checking out the latest CurrentWare how-to video. Today we will cover how to monitor application activity on your employee’s computers.
If you like this or other videos we’ve produced, hit the subscribe button below. Stay tuned to the end to learn how to get a free trial of the software I demo today.
The benefits of monitoring computer applications
Let’s get started with covering some of the benefits of monitoring application activity in your workplace.
- The first is Shadow IT and getting insight into unknown and unmanaged applications.
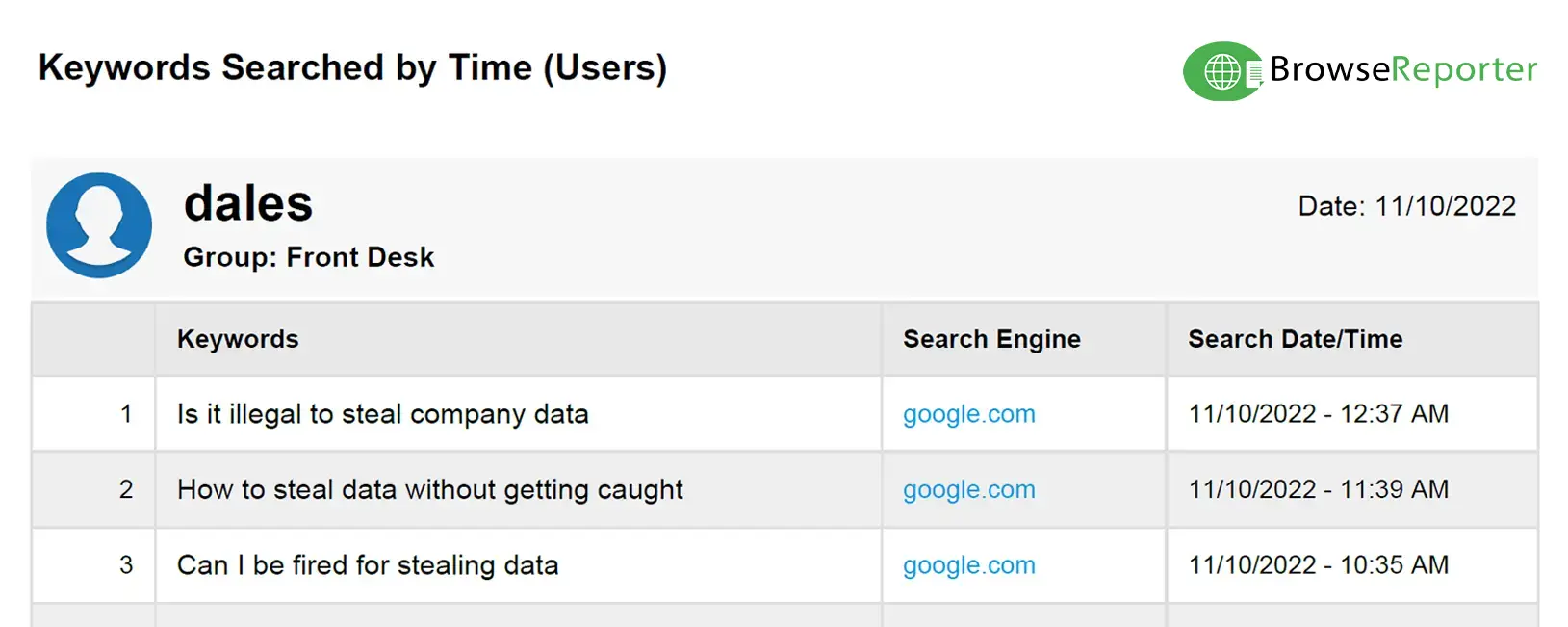
- The second is understanding who is using unproductive or non-work related programs.
- The third is Application Sprawl & License Management to see if there’s apps that very few users are using or legacy apps that should be removed & de-licensed
So let’s jump in.
Shadow IT refers to software that employees use without the knowledge of the IT department or management. According to the Everest Group over 50% of technology spend in organizations is considered Shadow IT. This means that over half their budgets are spent on software and programs that the IT department has no knowledge of.
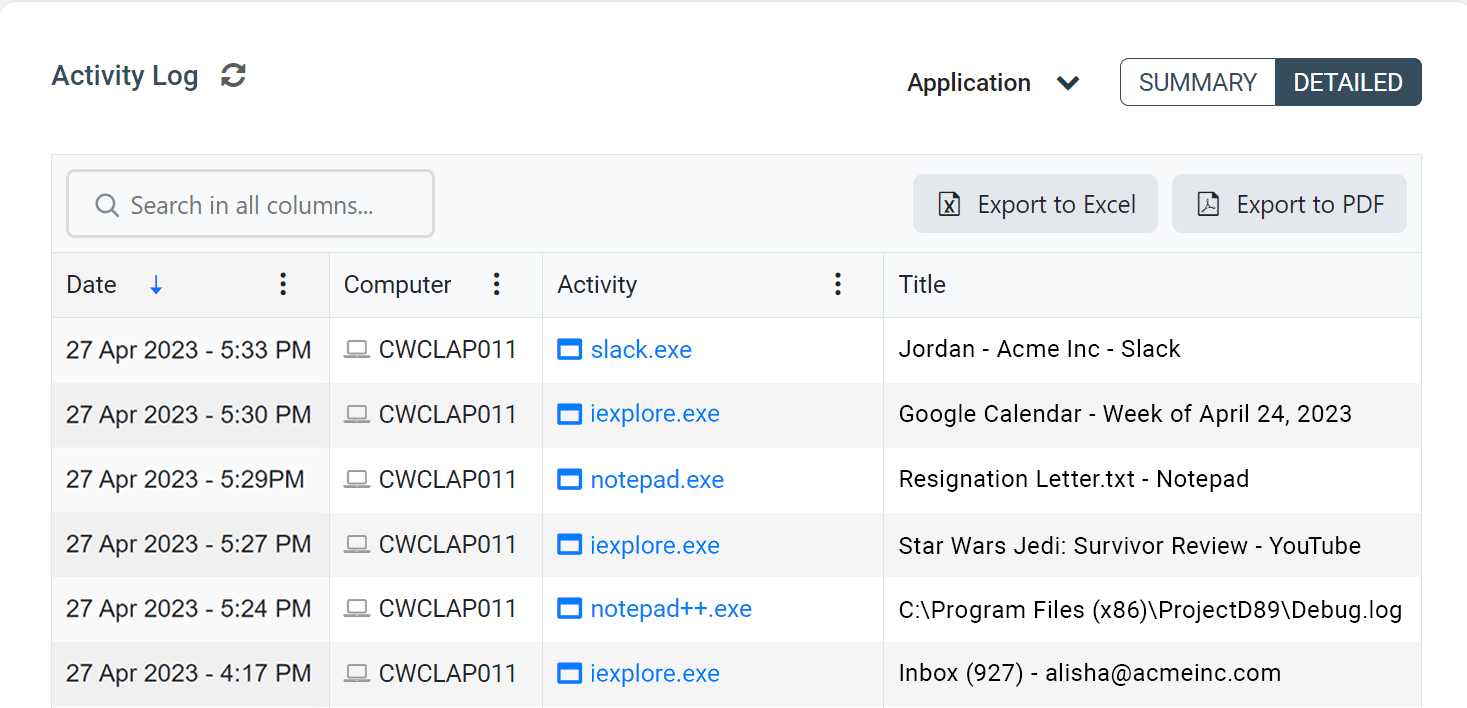
Monitoring application use with BrowseReporter
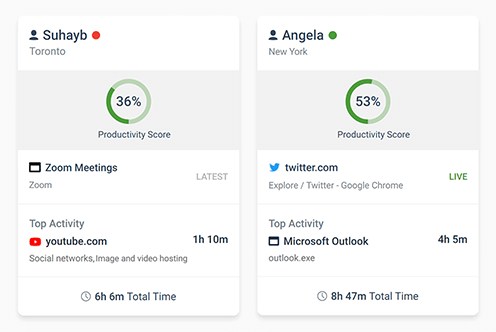
With CurrentWare’s BrowseReporter solution, you can see exactly which applications are being run in your environment.
In this example, we see that the user has the Dropbox app installed. Dropbox is a popular consumer cloud storage and sharing platform and the user has been using Dropbox to transfer and store files. In this company’s environment, Dropbox is not an approved file storage application so it is a major concern that they are using this application on a work device.
With BrowseReporter’s top applications by active time report, we are able to discover that the user Andy has been spending a significant amount of time on Dropbox as it’s his most used application. This is an issue that should immediately be investigated by the IT department to ensure the user is not involved in any nefarious activity.
In previous videos, we’ve covered how distracting and unproductive the internet can be, but applications can be just as bad. By using BrowseReporter, you can investigate which employees are being distracted by unproductive computer programs like chat apps, video games or movie players.
In this example, we can see the user is sending a lot of messages on Skype and by looking at the applications used by hour report, we see Andy spent all his time from 11AM and 1PM on Skype. Skype is not an application that is used by this organization for work purposes. This isn’t a productive use of Andy’s time and could be a good opportunity to speak to him about why he is spending so much time on the app.
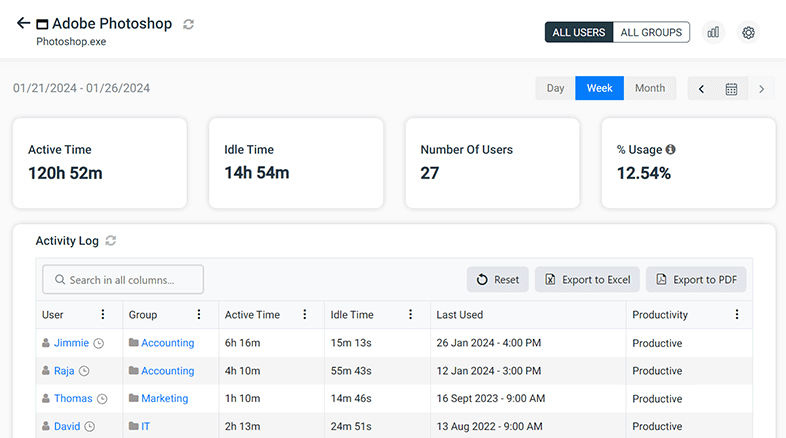
Collect software utilization data to address application sprawl
The third area to focus on is application sprawl and understanding software utilization. Software licenses, especially SAAS products can be expensive so understanding which products are actually being used by which employees can significantly reduce costs & cybersecurity risks. In addition, it’s a good opportunity to learn if there are products that some users are using that could benefit the rest of the organization.
In this example, we see that Andy has been using numerous different types of conference call, screen sharing and video applications like Go to Meeting, Slack, Zoho Assist, Zoho Meetings and Skype. All of these apps have similar functionality, so understanding why Andy is using so many different applications and whether these platforms should be blocked in our environment should be investigated. In addition, the IT department could understand the benefits of the platforms Andy is using and decide whether the tools can be deployed for the rest of the organization.
Block Windows Applications With BrowseControl
Now that we’ve covered how to monitor application activity, one last thing to note is undesirable applications can actually be blocked using CurrentWare’s BrowseControl. So whether it’s for security, productivity or for some other reason, being able to block applications that are not authorized for your environment can be beneficial.
With CurrentWare’s products you can also find out which URLs are being visited and block specific URLs or categories of websites. For example if Andy was also using dropbox.com or another cloud storage website, you can find out how often he was visiting that domain, block the URL, or even block the entire cloud storage category of websites.
Thanks for watching this video on how to monitor application use with BrowseReporter. If you have any thoughts on the reports or suggestions we’ve covered in this video, feel free to comment below.
If you’d like to give BrowseReporter or any of the other CurrentWare Solutions a try, please check out our free trial at CurrentWare.com/download or get in touch with us and we’d be happy to help!