What Is a Cybersecurity Audit? 7 Tips for Passing Your Next Audit and Meeting Compliance

Are you ready for your next cybersecurity audits? A report from Netwrix found that organizations consider themselves to be a mere 60% ready for an unexpected compliance check. Don’t let this be true for your organization; follow these tips to stay audit-ready at all times.
Key Takeaways
- Cybersecurity isn’t a checklist; meeting security compliance standards comes hand-in-hand with implementing appropriate safeguards.
- Security auditing needs to be an ongoing process. New threats and vulnerabilities are constantly emerging; meeting compliance objectives is only part of the picture.
- Internal audits are essential for ensuring that your organization is fulfilling its security responsibilities well before an external compliance audit.
- Inventory Your Existing Assets
- Identify the Potential Threats and Vulnerabilities for Each Asset
- Identify Existing Security Controls & Areas for Improvement
- Understand What the Auditor Is Looking For
- Make IT Risk Assessments a Continuous Process
- Consider Leveraging Third-Party Providers
- Ensure That Staff Are Aware of Their Security Responsibilities
What Is a Security Audit?

A security audit is an evaluation of an organization’s security controls against pre-established criteria. These criteria are often related to security requirements of legislation such as GDPR, HIPAA, and FISMA.
Types of cybersecurity audits include
- One-time assessments to address the needs of special events such as the introduction of new software (risk assessments, vulnerability assessments, etc)
- Regularly scheduled audits to verify that current capabilities and processes continue to meet internal and regulatory compliance requirements.
What Is the Main Purpose and Benefits of a Cybersecurity Audit?
Cybersecurity is all about understanding, managing, controlling, and mitigating the risks to critical assets. An IT compliance audit ensures that an organization is intimately aware of its current limitations and capabilities for managing security vulnerabilities.
The level of risk awareness provided by audits and assessments is essential for ensuring that an organization is meeting its compliance requirements.
For example, article 30 of the General Data Protection Regulation (GDPR) and section 1798.100 of the California Consumer Privacy Act (CCPA) require organizations to keep track of the personal data they gather and ensure that it’s stored and used within the stated purposes of its collection.
A Netwrix report notes that the majority of CIOs (71%) and CISOs (73%) they surveyed consider poor visibility into what data is being created or acquired to be a cybersecurity and compliance risk. Regular assessments of security and privacy controls help organizations ensure that regulated data is being collected, stored, and processed appropriately.
Cybersecurity audits help to:
- Assess whether or not the organization’s existing security posture is capable of addressing threats within the cybersecurity landscape
- Verify that current efforts are meeting their objectives (efficacy of security training, providing staff with secure tools for business processes, etc)
- Discover IT assets that need to be decommissioned or upgraded
- Ensure that the organization is meeting its security requirements by identifying areas of risk for noncompliance.
- Prove to stakeholders (such as potential investors) that the organization has an adequate security posture
Organizations that fail to perform continuous security risk assessments and audits have a greater risk of data breaches and failed compliance audits. These security incidents are incredibly damaging to a company’s reputation, business continuity, and the security/privacy of their data subjects.
FREE GUIDE & CHECKLIST
How to Keep Data Safe When Offboarding Employees
The employee offboarding process presents significant data security risks. Employees have intimate access to corporate data, insider knowledge of the organization’s systems, and a level of trust that can allow them to steal data undetected.
Click the button below to learn the best practices for managing insider threat risks during offboarding & gain access to a checklist of key cybersecurity items you must include in your offboarding process.
7 Tips to Help You Pass Your Cybersecurity Audit
This section will provide you with steps you can take to ensure that your organization meets its compliance requirements.
The majority of these tips center around conducting self-evaluations. Regular internal audits are essential for ensuring that your organization is meeting compliance standards before being assessed by an external auditor.
Regular internal audits are a requirement for some security frameworks. For example, HIPAA requires that covered entities conduct a “risk analysis” to meet the requirements of the HIPAA security rule.
“Risk analysis should be an ongoing process, in which a covered entity regularly reviews its records to track access to e-PHI and detect security incidents, periodically evaluates the effectiveness of security measures put in place, and regularly reevaluates potential risks to e-PHI.”
HIPAA Security Rule, sections 164.306–308
These audits are intended to “conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by the [organization].”
Naturally, this process is going to involve a plethora of documentation.
Thorough documentation is paramount to proving to a compliance auditor that your organization is taking the necessary measures to meet compliance requirements.
Depending on your framework you may need to provide auditors with evidence of compliance going back several years. This could include firewall reports, penetration testing results, security event logs, company policies, past risk assessments, you name it.
Keeping these robust reports well organized alongside your checklists and other documentation is going to make conducting regular IT risk assessments and internal audits a lot easier.
With that said, let’s get into the tips…
1) Inventory Your Existing Assets

When conducting a security audit the first step is to inventory the organization’s assets. Having a clear understanding of what is currently in use will provide a clear picture of what assets need to be protected, any associated vulnerabilities, and what controls your organization has to protect them.
During this step, you’ll want to ensure you find and document every IT asset in your organization. A proper risk analysis must cover every relevant asset including software, regulated data, databases, servers, workstations, security devices, and associated business processes.
Depending on the size of your organization this process may need to be facilitated with IT asset management (ITAM) software.
IT Asset Management Tips
- Review purchase orders, existing inventory logs, ITAM reports, and the premises for existing hardware and software
- Monitor software usage and internet activity to identify shadow IT programs and cloud services that can be replaced with sanctioned alternatives
- Consult with senior management to track down any assets that have been unknowingly acquired since the last inventory check
- Review your organization’s bring-your-own-device (BYOD) policies to understand how personal devices are being used within your infrastructure
2) Identify the Potential Threats and Vulnerabilities for Each Asset

“The overwhelming majority of organizations (91%) claim they store sensitive and regulated data only in secure locations. However, this confidence is clearly misplaced, since 24% of them admitted discovering such data outside of designated secure locations in the past year… About the same percentage of them reported that their IT staff granted direct access to sensitive and regulated data based solely on a user’s request in the past year. Not surprisingly, 54% of these organizations suffered audit findings and fines for non-compliance.”
2020 Data Risk & Security Report, Netwrix
Now that you’re prepared with a detailed inventory of your existing assets, it’s time to understand the threats and vulnerabilities they have.
Each security risk your organization faces will have..
- An asset to protect
- A threat that could exploit the assets
- Vulnerabilities that make an exploit feasible
Understanding how your existing infrastructure could be damaged or exploited is essential for mitigating any potential risks.
Using a cybersecurity framework such as the NIST RMF (National Institute of Standards and Technology’s Risk Management Framework) is valuable for ensuring that your internal assessments and audits address the key elements of risk that your organization could face.
The RMF consists of 7 steps to help an organization select the appropriate security controls
- Prepare the organization to manage security and privacy risks
- Categorize the system and information processed, stored, and transmitted based on an impact analysis
- Select the set of NIST controls to protect the system based on risk assessment(s)
- Implement the controls and document how controls are deployed
- Assess to determine if the controls are in place, operating as intended, and producing the desired results
- Authorize the system to operate (following a risk-based decision from a senior official)
- Monitor the control implementation and risks to the system continuously
While the NIST RMF doesn’t tell you how to achieve the recommended steps, it does provide valuable guidance to help your organization focus on the most critical security considerations.
Benefits of following a cybersecurity framework
- Provides a better understanding of accepted risks and those that will be remediated
- Improves focus on areas that matter most to the organization’s security
- Facilitates IT risk management decisions
- Helps an organization meet security and privacy compliance requirements
What are threats and vulnerabilities?
A vulnerability is a flaw that could be exploited by a threat to compromise an asset. You can think of a vulnerability as the “why” or “how” in a risk assessment.
A threat is any actor that could exploit a vulnerability to negatively affect the confidentiality, integrity, or availability of an asset. You can think of a threat as the “what” or “who” in a risk assessment.
For example, Netwrix research found that departing employees were responsible for 39% of intellectual property theft incidents in 2018. That very same report notes that 44% of respondents do not know what their employees are doing with sensitive data.
A disgruntled employee is a significant threat as they can exploit a vulnerability such as unrestricted access to portable storage hardware to steal sensitive information after an involuntary termination.
Other examples of threats vs vulnerabilities
- A lack of security policies, processes, and procedures makes the organization vulnerable to negligent insider threats
- A lack of offsite backups makes the organization vulnerable to physical threats such as floods and fires
- A mobile endpoint in an unlocked car is a significant physical security vulnerability as a threat actor could easily steal it.
3) Identify Existing Security Controls & Areas for Improvement

If you’re expecting a cybersecurity audit, it’s no doubt that your organization already has existing safeguards to protect the confidentiality, integrity, and availability of your systems and information.
The real question is are your existing security controls sufficient for meeting compliance requirements?
Consider this
- 54% of organizations ignore the security best practice of reviewing access rights to data on a regular basis. (2020 Netwrix Data Risk & Security Report)
- Among organizations who don’t check access rights to archived data regularly, 52% reported a compromise of that data during the past 12 months (2020 Netwrix Data Risk & Security Report)
- Only 17% of organizations have an approved incident response plan and make sure this plan works by conducting test runs and providing training for employees (2018 Netwrix IT Risks Report)
In this next step, you will take the threats and vulnerabilities outlined in the previous step, identify your existing security controls, and prioritize any remediation needed.
| Threat/Vulnerability | Security Controls |
| Insider data theft | Data loss prevention (DLP) and device control software to monitor and restrict data exfiltration. |
| Phishing and social engineering | Security awareness training for users, email security gateways, and administrative safeguards such as policies, processes, and procedures |
| High-risk internet browsing and other Web-based threats | Web filters and firewalls to restrict internet traffic, user activity monitoring solutions to ensure that systems are used safely and appropriately |
| Off-site employees with remote access to internal resources | Risk-based multi-factor authentication, a VPN with posture assessment features, and controls to prevent data transfer to mobile endpoints. |
| third-party tools, vendors, and/or contractors with a connection to our internal systems | A Business Associates Agreement (BAA) that stipulates security requirements of third parties, monitoring solutions to alert of suspicious activity, limiting access to sensitive assets as much as possible. |
| Compromised user credentials | Risk-based multi-factor authentication, limiting user privileges as much as possible, monitoring user activity. |
As you go through this process you will discover which security risks are being effectively addressed and what capabilities need to be added to ensure that any outstanding threats are mitigated.
Your risk management framework and security compliance requirements will further dictate the measures you need to take.
How to Prioritize New Security Controls
There’s no doubt that your risk assessment is going to find a vast number of potential vulnerabilities. Realistically you will not be able to mitigate every possible risk to your organization; that’s where prioritization comes in.
Since you cannot realistically safeguard against everything, you need to be prepared to prove to security auditors that you’ve taken all of the reasonable measures necessary to protect the sensitive data in your custody.
Reasonable measures involve identifying plausible risks, assessing their likelihood and impact, and ensuring that you’ve addressed the highest priority risks. Any risks that cannot be entirely eliminated must be documented with a legitimate reason for the limitation in your security plan.
A risk matrix is a helpful tool for prioritizing risks; it allows you to describe the organization’s risk factors, your intended security strategy outcomes, and how the strategy’s outcomes are either being met or not met by existing security controls.
In your risk matrix, you will outline all of the potential vulnerabilities and threats, as well as the security controls that are available to address them.
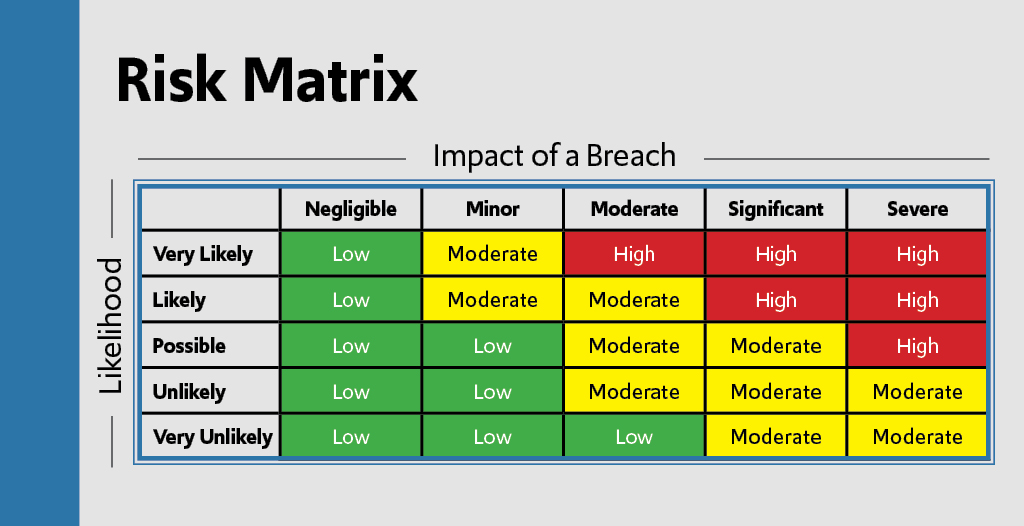
The risk category for a given asset is classified based on
- The severity of the impact should it be compromised
- The likelihood that the device will be compromised
- The controls that are available to mitigate the risk
Naturally, assets with a higher risk category need to be prioritized first.
FREE Employee Offboarding Checklist Template—Prevent Data Theft by Departing Employees
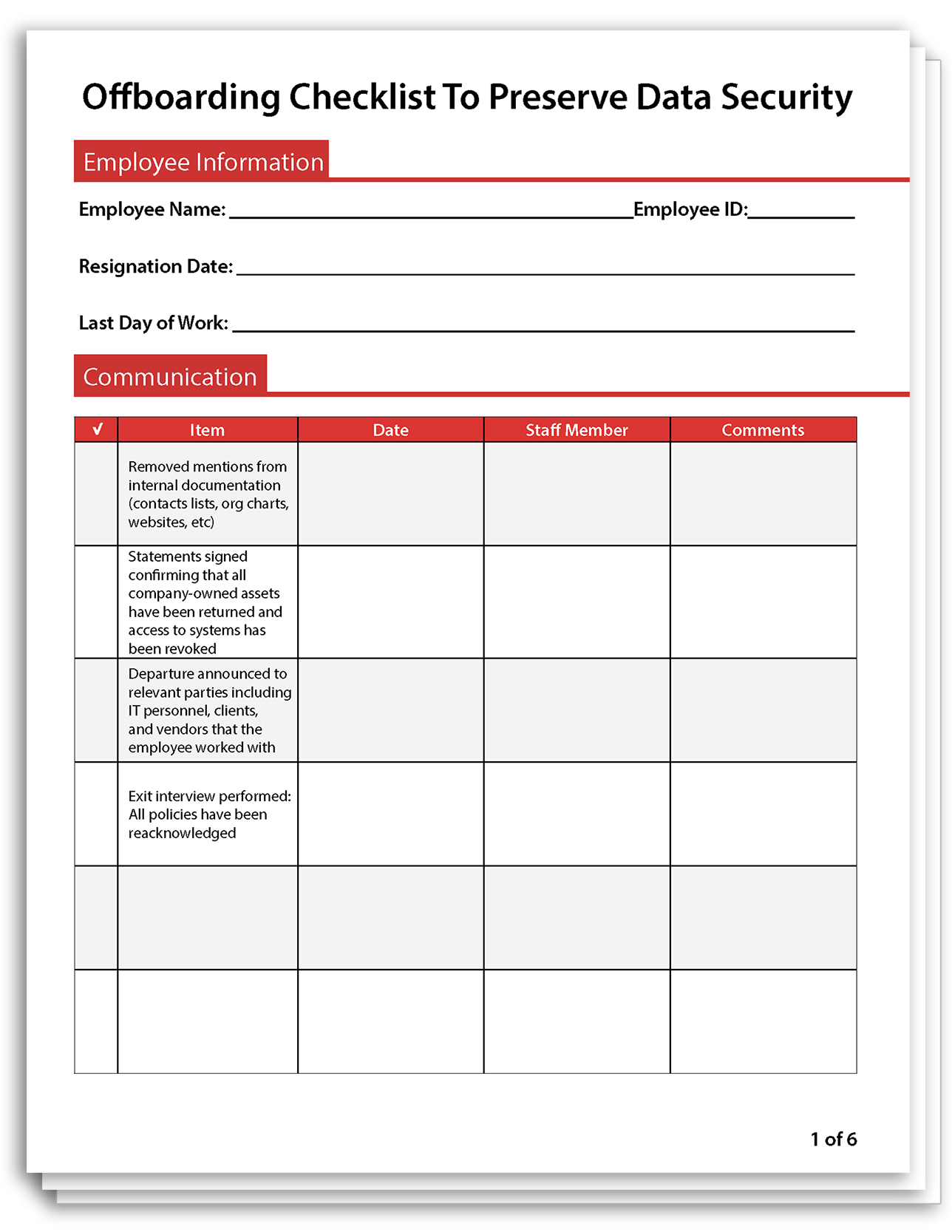
Concerned about the damage a soon-to-be-ex-employee could cause with access to IP, passwords, and other sensitive data?
Follow this employee offboarding checklist to protect your organization against insider data theft.
4) Understand What the Auditor Is Looking For
The role of a security auditor is to offer an objective perspective of your organization’s security practices. They will work with your internal executives, managers, and IT professionals to ensure that your organization is as secure and compliant as it possibly can be.
What a security auditor is looking for shouldn’t be too much of a surprise. Having a clear understanding of your organization’s framework(s) and regulations will go a long way to anticipating what they will be looking for.
Here’s what an external auditor will want to know
- What sensitive data are you responsible for? (PII, PHI, credit card information, etc)
- What measures do you currently take to protect sensitive data throughout its lifecycle (creation, storage, usage, archiving, and disposal)
- How are your current security controls meeting the security and privacy requirements of the protected assets?
To improve the efficacy of your internal assessments, consider reaching out to your auditor in advance. They may be willing to provide you with the risk assessment checklists and other documents that they’ll be using as a part of their process.
5) Make IT Risk Assessments a Continuous Process

Netwrix research found that though 70% of companies are already doing risk assessments, the majority of them do not do it regularly.
Meeting (or exceeding!) security standards must be a priority throughout your entire organization.
Risk assessments simply aren’t a one-and-done deal; identifying and mitigating risks needs to be a continuous process to ensure that your organization is prepared to address new threats as they arise.
How often should IT risk assessments be done? The recommended best practice is to re-evaluate your risks at least every one to three years. This ensures that your security controls remain adequate as your IT assets change and new threats and vulnerabilities emerge.
If security isn’t prioritized by business leaders, meeting compliance standards will be an uphill battle.
- Employees take cues from senior leadership; if security isn’t a priority for their bosses, it’s much more likely that it won’t be a priority for them either.
- If the IT department is treated as a cost center (rather than a revenue/capability multiplier), critical security upgrades won’t get the support they need to be deployed and managed properly.
- If security compliance requirements are treated as a legal obligation and a checkbox the organization risks falling behind on mitigating against the latest vulnerabilities and threats.
A lack of involvement from senior management was a problem for 32% of IT pros surveyed for the 2017 Netwrix IT Risks Report. These IT pros needed buy-in from business leaders to get the budget and support they needed for new security measures or personnel.
Risk assessments are an excellent way to increase buy-in; they’ll clearly outline what security gaps the organization has, what upgrades are required to address those gaps, and the impact a breach would have on those assets. This data is paramount for justifying IT budgets, particularly if the need for the upgrades is not immediately apparent to non-IT personnel.
6) Consider Leveraging Third-Party Providers

Depending on your organization’s needs and resources you may want to consider hiring a managed security service provider (MSSP) that is familiar with the security controls required by your organization’s frameworks and regulations.
The main benefit of internal IT services is having employees on staff who understand the unique needs of your organization. While dedicated personnel is highly desirable, it’s not always feasible—particularly for specialized tasks such as internal compliance audits and interpreting logs from security information and event management (SIEM) solutions.
Even if your organization already has internal capabilities to help manage day-to-day operations, leveraging the capabilities and expertise of a third-party can provide significant benefits.
The advantages of third parties
- An audit from a disinterested third-party will provide more objective opinions than one from an internal stakeholder
- Third-party security consultants can fix specific issues efficiently, allowing your staff to focus on their core competencies
- An experienced security auditor can help ensure that your organization implements a successful audit
Regardless of whether you use internal or external capabilities, at the end of the day, someone needs to be held responsible for ensuring that your organization has the capabilities in place to meet its security requirements.
Ultimately, this duty falls on management.
IT security teams are a valuable resource for implementing controls and maintaining assets, but they need support from management to make it happen.
Outsourcing security doesn’t remove the responsibility of management, either. Once security controls are in place management still needs to take measures to ensure that policies and procedures are being followed by all staff.
7) Ensure That Staff Are Aware of Their Security Responsibilities

Security policies, processes, and procedures are simply non-negotiable. When equipped with the right training and support, employees are a valuable asset for protecting sensitive data.
While the type and detail of training may vary depending on the risk level of their roles, every staff member with access to IT assets needs some form of security awareness training. The organization also needs processes and procedures that dictate the best practices that staff must follow.
Why are security policies, processes, and procedures so critical?
Having well-trained staff greatly reduces the likelihood of security vulnerabilities such as improper data handling procedures, engaging in high-risk computer activity, and falling for social engineering tricks from malicious threat actors.
Knowledgeable employees not only make far fewer security mistakes—they also help identify suspicious activity so it can be dealt with before it leads to a data breach.
Prioritizing security in this way is also essential for cultivating a culture of compliance within the company. Investing in regular security training (and adhering to the requirements) communicates the importance of compliance to everyone involved.
Leadership is responsible for ensuring that the staff takes their security responsibilities seriously. It must be made clear from day 1 what standards the organization adheres to, why those standards are critical, and the staff’s role in ensuring those standards are met.
Best practices for providing end-users with security training
- Assign someone to be directly responsible for ensuring that the staff is educated about their security responsibilities.
- If security expertise is not available internally, contract a cybersecurity awareness training consultant.
- Ensure that any security training includes some form of testing to identify areas where staff may require additional training.
- Provide staff with retraining every 4-6 months to ensure that they remain aware of their risks and responsibilities.
- Maintain an open communication policy that allows employees to ask questions when they are uncertain of the best course of action.
Conclusion & More Resources
- Gartner – Strategic Planning for Audit
This guide from Gartner provides insights on how to develop a concise and compelling audit strategy, best-practice examples of how to plot your strategic plan, and customizable templates to communicate your plan to internal stakeholders and partners. - Canadian Centre for Cyber Security – Cybersecurity Audit Program
The Cyber Security Audit Program is part of a series of free tools for auditors to use to assess the cyber security status of their organizations. It includes a one-page overview of cyber security audit criteria, an audit guide, tools to assess your organization’s overall cyber security status, and a detailed document for outlining the audit criteria for many types of cyber security audits. - U.S. Department of Health & Human Services (HHS) – Guidance on Risk Analysis
Organizations that are subject to HIPAA are required to conduct regular risk analyses. Even if your organization is not a covered entity under HIPAA, this page provides valuable guidance for conducting your own IT risk assessment. - CurrentWare – Cybersecurity Guide for Small Businesses with a Limited Budget
Cybersecurity for small businesses doesn’t have to be expensive, but it is critical. According to Verizon research, 43% of reported data breaches involved small business victims. Follow this guide to keep your business secure without breaking the bank. - CurrentWare – USB Drive Security Best Practices
This blog post covers USB security best practices to equip you with the knowledge to safeguard your company’s valuable information against the security risks of removable media devices such as flash drives.